Deepfake & AI Detection
Welcome to Impersonation Prevention Community
Latest Posts
- AI-driven Cybersecurity
- Application & Code Security
- Authentication & MFA Security
- Cloud Security
- Compliance & Reporting
- Critical Infrastructure Security
- Data Security & Privacy
- Deepfake & AI Detection
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Enterprise Collaboration Security
- Enterprise Cybersecurity
- Executive & VIP Protection
- Financial & Crypto Security
- Healthcare Security
- Hiring & Onboarding Security
- Identity & Access Management
- Identity Fraud Prevention
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- Remote Work Security
- Security Automation (SOAR)
- Security Awareness & Training
- Social Engineering Prevention
- Third-Party & Vendor Security
- Threat Intelligence
- Threat Intelligence & Prevention
- Vulnerability & Risk Management

Deepfake Disruption of Corporate Board Votes
Tackling the Threat of AI-Driven Deceptions in Corporate Board Votes What if your company’s board decisions were manipulated by parties with malicious intent? Where a board vote fraudulently swayed the balance of power or a
Read more
Deepfake Sabotage of Company Earnings Calls
The Growing Threat of Deepfake Sabotage in Corporate Communications How prepared are businesses for the alarming rise of deepfake technology? Let’s explore how this innovative tool, while offering countless opportunities, also presents significant threats, particularly
Read more
Defeating 3D Face Masks with Depth Sensing
By Ava Mitchell |
Critical Infrastructure SecurityDeepfake & AI DetectionIdentity & Access Management
Enhancing Security with Depth Sensing: A Robust Approach to 3D Mask Detection Have you ever wondered how advanced technology is being used to tackle the sophisticated threats of identity fraud and social engineering? With technology
Read more
Deepfake Ransomware Negotiations
Understanding the Threat of AI-Driven Social Engineering Are organizations prepared to combat the growing threat of fake ransom negotiators and synthetic extortion? The rise of artificial intelligence (AI) has revolutionized industries, but it has also
Read more
Deepfake Sabotage of PR Announcements
The Rising Threat of Synthetic PR Fraud How often have we relied on digital communication for crucial announcements? Where digital communication is the backbone, the emergence of synthetic public relations (PR) fraud presents an unprecedented
Read more
Bypassing Biometrics with Master Prints
By Brooke Lawson |
Deepfake & AI DetectionIdentity & Access ManagementVulnerability & Risk Management
The Evolving Threat of Biometric Master Prints: A Silent Challenge How well do you trust the security systems that guard your organization’s digital assets? The belief that biometric systems—like fingerprint and facial recognition—offer infallible protection
Read more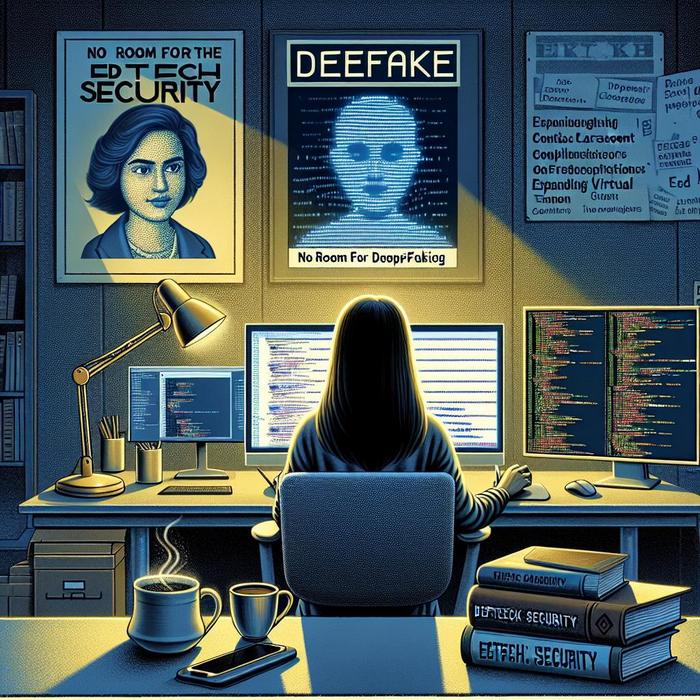
Deepfake Infiltration of Virtual Classrooms
The Evolution of EdTech Security in Deepfake Threats Have you ever wondered how advanced artificial intelligence (AI) technology could potentially compromise the safety and security of educational environments? With the rise of AI-driven deepfakes, education
Read more
High-Fidelity Biometrics for Remote High-Security
Securing the Future with High-Fidelity Biometrics How can organizations elevate their digital defenses against sophisticated AI-driven threats? With cyber threats evolve, so too must the strategies companies employ to protect themselves. The deployment of high-fidelity
Read more
Deepfake Blackmail of Corporate Leaders
The Rising Threat of AI-Powered Synthetic Media in Executive Extortion How do organizations safeguard their digital integrity against the ominous wave of synthetic media blackmail? With AI technology advancing at unprecedented rates, cybersecurity professionals are
Read more
Weaponized Deepfakes in Geopolitical Conflict
Understanding the Rise of Weaponized Deepfakes in Modern Conflict How do sophisticated AI-driven deepfakes shape modern geopolitical conflicts? Disinformation campaigns have evolved dramatically with the advent of AI technology, enabling state-sponsored entities to conduct deceptive
Read more
Liveness Checks for High-Value Wire Transfers
The Critical Role of Liveness Checks in High-Value Wire Transfers How secure are your wire transfers? This question is at the forefront of every organization’s mind, particularly when dealing with high-value transactions. The increasing sophistication
Read more
Protecting the Password Reset Flow from Deepfakes
Is Your Password Reset Process Safe from Deepfake Threats? Where security is paramount, organizations face evolving challenges. Deepfake technology is now at the forefront of these concerns, posing a significant threat to traditional password reset
Read more
Certifying Real Human Content
Understanding the Imperative of Human Identity in AI Have you ever paused to consider how your organization verifies the authenticity of its digital interactions? With artificial intelligence (AI) capabilities continue to evolve, the need for
Read more
Continuous Liveness Monitoring in High-Risk Sessions
Building Trust Through Continuous Liveness Monitoring Have you ever wondered how digital identity integrity can be maintained where AI-driven deception tactics are advancing at a rapid pace? Integrating effective measures like continuous liveness monitoring is
Read more
When Your CISO is Deepfaked
The Unseen Threat: AI-Driven CISO Impersonation and Its Ramifications Is your organization prepared to face a cybersecurity threat that is as invisible as it is sophisticated? With technology evolves, so too do the methods of
Read more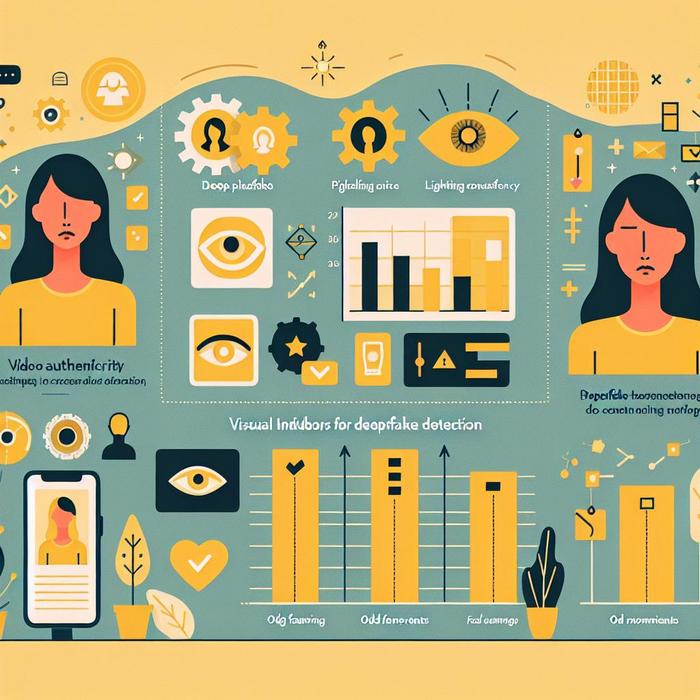
Visual Indicators for Deepfake Detection
Understanding AI-Driven Identity Threats How can organizations effectively combat the sophisticated threats posed by AI-driven fake content? With an industry specialist, the focus on identity verification is paramount for professionals across various sectors. The growing
Read more
Analyzing Voice Pitch in Vishing Attacks
Understanding the Role of Voice Frequency Analysis in Combatting Vishing Attacks How can organizations fortify their defenses against the burgeoning threat of vishing attacks, especially in mission-critical sectors? Cybersecurity professionals are increasingly turning to advanced
Read more