Enterprise Collaboration Security
Welcome to Impersonation Prevention Community
Main Community
Latest Posts
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security

Simulating Deepfake Infiltration in All-Hands
By Dylan Keane |
Deepfake & AI DetectionEnterprise Collaboration SecuritySecurity Awareness & Training
Understanding the Threat of Deepfake Infiltration Could your next corporate meeting become a target for deepfake technology? The rapid advancement of AI has led to the emergence of more sophisticated and audacious threats, particularly when
Read more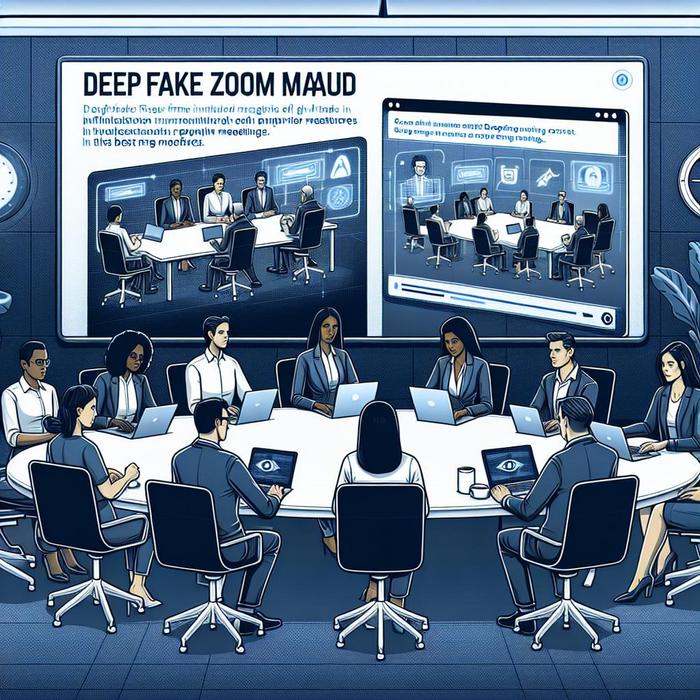
Simulation of Deepfake Infiltration in All-Hands Meetings
By Dylan Keane |
Enterprise Collaboration SecuritySecurity Awareness & TrainingDeepfake & AI Detection
Understanding Threats AI-Driven Deceptive Practices Have you ever considered how vulnerable your corporate meetings are to the rapidly evolving threats posed by AI-driven technology? Safeguarding the integrity of corporate interactions is more imperative than ever.
Read more
Deepfake Infiltration of Virtual Classrooms
The Evolution of EdTech Security in Deepfake Threats Have you ever wondered how advanced artificial intelligence (AI) technology could potentially compromise the safety and security of educational environments? With the rise of AI-driven deepfakes, education
Read more