Malware & Botnet Security
Welcome to Impersonation Prevention Community
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security

Self-Optimizing Impersonation Botnets
Rising to the Challenge: Outsmarting Autonomous Scam Bots Have you ever wondered how modern organizations can combat the rising tide of artificial intelligence (AI)-driven fraud? With technology rapidly advances, so too does the sophistication of
Read more
The Scale of Automated Identity Harvesting
Evolving Threats AI-Driven Identity Harvesting What happens when identity harvesting bots infiltrate your digital? Identity theft is not a novel concept, but the methods used to execute these attacks have become alarmingly sophisticated. Automated credential
Read more
Hardening the New User Registration Pipeline against Bots
Recognizing Evolving Threats in User Registration How can organizations stay ahead of evolving threats in securing user registration processes? With cybercriminals leveraging AI to create sophisticated deepfakes and launch multi-channel social engineering attacks, the stakes
Read more
Fake IT System Update Alerts via Push Notification
By Kelsey Jones |
Malware & Botnet SecurityIT & Help Desk SecurityEndpoint Detection & Response (EDR/XDR)
Understanding Threats Malicious Updates How do organizations safeguard their IT infrastructure against deceptive tactics like fake system update alerts? This question is increasingly critical for businesses across sectors, especially with sophisticated cyber threats evolve. One
Read more
The Evolution of Identity Fraud Markets
Understanding Identity Fraud Could your organization fall prey to mass identity fraud? While we delve into evolving digital security, one cannot ignore the growing sophistication of identity fraud markets. Where every click, chat, and transaction
Read more
The Industrialization of Synthetic Persona Farms
How Do Identity Bot Farms Threaten Our Security Frameworks? Safeguarding identity and access management (IAM) is pivotal where threat actors employ synthetic identities at scale to breach corporate defenses. These synthetic identity scale operations—often referred
Read more
Hardening the User Registration Pipeline
Enhancing the User Registration Pipeline Against AI-Driven Threats Have you ever pondered the vulnerabilities inherent in your company’s user registration process and the ways that AI-driven threats might exploit them? Where cybercriminals constantly refine their
Read more
Fake Urgent Security Patch Email Phishing
Understanding the Risks of Emergency Patch Scams How secure is your organization against AI-driven threats masquerading as legitimate communications? A new breed of scams—such as emergency patch scams—aims to exploit vulnerabilities quickly and effectively. These
Read more
Fake IT System Update Notifications
By Jordan Pierce |
IT & Help Desk SecurityEndpoint Detection & Response (EDR/XDR)Malware & Botnet Security
Understanding the Threat: Sophisticated Impersonation in IT System Updates Have you ever wondered if that IT system update email was the real deal? If you hesitated even for a second, you’re not alone. With cybercriminals
Read more
The Industrialization of Identity Theft
Understanding the Unseen Threat: Mass Identity Fraud in AI Have you considered how mass identity fraud is evolving ? With digital interactions become increasingly woven into the fabric of our daily lives, threats has radically
Read more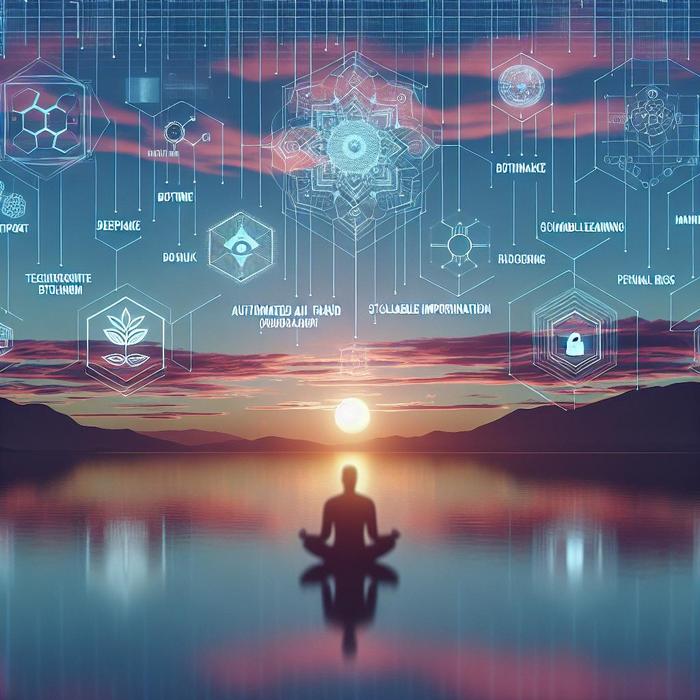
Deepfake Botnets: Automated Mass Impersonation
Embedding Trust in Digital Communications: A Proactive Approach to Deepfake Botnets How prepared is your organization for the inevitable advances in AI-driven threats, particularly with the rise of deepfake botnets and automated AI fraud? These
Read more
AI vs AI Security Battles
By Madison Clarke |
AI-driven CybersecurityThreat Intelligence & PreventionMalware & Botnet Security
Empowering Organizations in AI Security Battles Have you ever wondered how organizations protect themselves of AI-driven attacks? Digital is burgeoning with advanced technologies that, while transformative, also open the gateway to complex threats. Identity verification
Read more
Deepfake-as-a-Service (DaaS)
Addressing AI-Driven Deception: Strategies for Secure Digital Interactions How can organizations protect themselves from the growing threat of deepfake technology? This pressing question faces modern Chief Information Security Officers (CISOs), Chief Information Officers (CIOs), and
Read more
Protecting Against Malware Delivered During Enrollment
Why Is Identity Verification Crucial in Combating Malware in Onboarding? Identity verification has become a linchpin in our digital defense strategies. With technology advances, so do the tactics of cybercriminals. These illicit actors are utilizing
Read more
Infostealer Malware: Gateway to Data Breaches
Threat Landscape: The Emerging Role of Infostealer Malware How prepared is your organization to address the rising wave of security threats? Digital is constantly evolving, and the adoption of sophisticated tools such as infostealer malware
Read more