Security Awareness & Training
Welcome to Impersonation Prevention Community
Main Community
Latest Posts
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security

Simulating Deepfake Infiltration in All-Hands
By Dylan Keane |
Deepfake & AI DetectionEnterprise Collaboration SecuritySecurity Awareness & Training
Understanding the Threat of Deepfake Infiltration Could your next corporate meeting become a target for deepfake technology? The rapid advancement of AI has led to the emergence of more sophisticated and audacious threats, particularly when
Read more
Simulating Executive Identity Breaches in Tabletop Exercises
Strengthening Cybersecurity Preparedness with Executive Breach Simulations How prepared are you to counteract a sophisticated identity breach? AI-driven threats are no longer the stuff of science fiction but a daunting reality that organizations across the
Read more
Building an Identity-Aware Developer Culture
Embracing Developer Identity Awareness in Cybersecurity Are you truly secure when it comes to safeguarding developer identities? The sophistication of AI-driven threats demands more than just basic protective measures. Where the guardians of sensitive data
Read more
Simulation of Deepfake Infiltration in All-Hands Meetings
By Dylan Keane |
Security Awareness & TrainingEnterprise Collaboration SecurityDeepfake & AI Detection
Understanding Threats AI-Driven Deceptive Practices Have you ever considered how vulnerable your corporate meetings are to the rapidly evolving threats posed by AI-driven technology? Safeguarding the integrity of corporate interactions is more imperative than ever.
Read more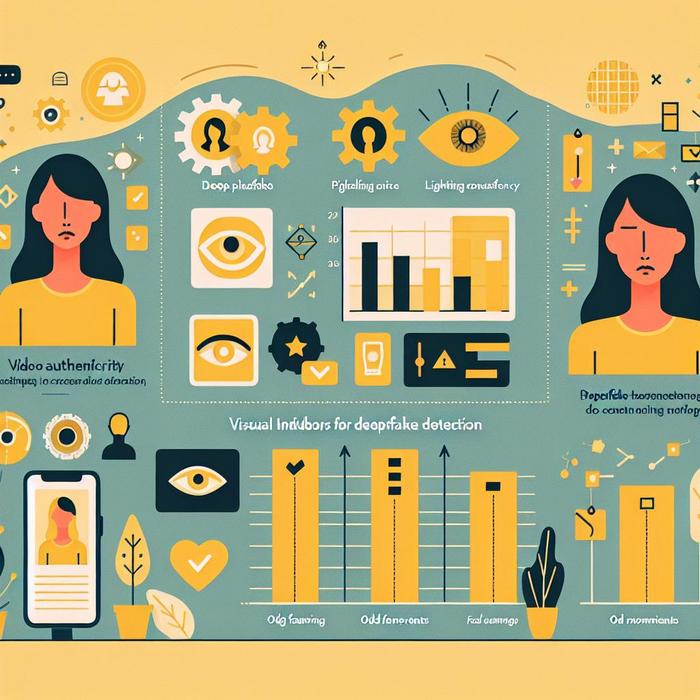
Visual Indicators for Deepfake Detection
Understanding AI-Driven Identity Threats How can organizations effectively combat the sophisticated threats posed by AI-driven fake content? With an industry specialist, the focus on identity verification is paramount for professionals across various sectors. The growing
Read more
Tabletop Exercises for Executive Impersonation
Reinforcing Digital Security Through Executive Impersonation Drills What if the next voice on your conference call wasn’t your CEO, but a sophisticated impersonation orchestrated by cybercriminals? The rise of AI-driven threats, including deepfake technology and
Read more
MFA Recovery Fatigue: The Help Desk Weak Link
Understanding the Challenge of Multi-Factor Authentication (MFA) Recovery Attacks What happens when the very protocols designed to protect our digital identities become the points of vulnerability? This paradox is particularly evident in MFA recovery attacks,
Read more
Help Desk Fatigue Reduction
Addressing Help Desk Challenges with Proactive Identity Verification Have you ever pondered the relentless pressures that help desk professionals face daily? Where cybersecurity threats are advancing at a rapid pace, ensuring identity trust has never
Read more
Impersonation Response Plan
Strategies to Safeguard Your Organization Against AI-Driven Threats Have you ever wondered how prepared your organization is to counteract sophisticated AI-driven threats? The growing potential of AI-powered cyberattacks demands urgent attention. These threats range from
Read more
Restore Seeing is Believing in the GenAI Era
How Can We Secure Verifiable Digital Identity? Imagine receiving a message that seems legitimate, only to realize it was a cleverly disguised deepfake or social engineering ploy. This unnerving reality is at the forefront of
Read more








