Deepfake & AI Detection
Welcome to Impersonation Prevention Community
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security
Weaponized Deepfakes in Geopolitical Conflict
Understanding the Rise of Weaponized Deepfakes in Modern Conflict How do sophisticated AI-driven deepfakes shape modern geopolitical conflicts? Disinformation campaigns have evolved dramatically with the advent of AI technology, enabling state-sponsored entities to conduct deceptive
Read more
Liveness Checks for High-Value Wire Transfers
The Critical Role of Liveness Checks in High-Value Wire Transfers How secure are your wire transfers? This question is at the forefront of every organization’s mind, particularly when dealing with high-value transactions. The increasing sophistication
Read more
Protecting the Password Reset Flow from Deepfakes
Is Your Password Reset Process Safe from Deepfake Threats? Where security is paramount, organizations face evolving challenges. Deepfake technology is now at the forefront of these concerns, posing a significant threat to traditional password reset
Read more
Certifying Real Human Content
Understanding the Imperative of Human Identity in AI Have you ever paused to consider how your organization verifies the authenticity of its digital interactions? With artificial intelligence (AI) capabilities continue to evolve, the need for
Read more
Continuous Liveness Monitoring in High-Risk Sessions
Building Trust Through Continuous Liveness Monitoring Have you ever wondered how digital identity integrity can be maintained where AI-driven deception tactics are advancing at a rapid pace? Integrating effective measures like continuous liveness monitoring is
Read more
When Your CISO is Deepfaked
The Unseen Threat: AI-Driven CISO Impersonation and Its Ramifications Is your organization prepared to face a cybersecurity threat that is as invisible as it is sophisticated? With technology evolves, so too do the methods of
Read more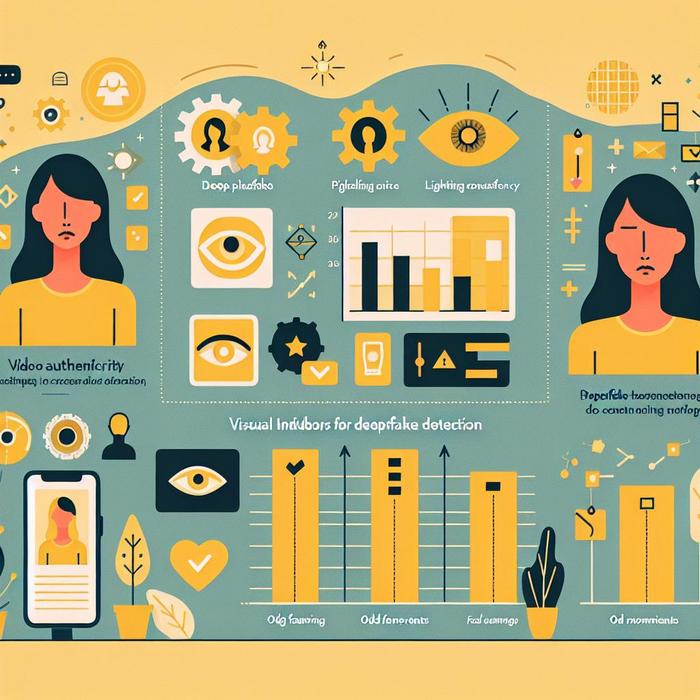
Visual Indicators for Deepfake Detection
Understanding AI-Driven Identity Threats How can organizations effectively combat the sophisticated threats posed by AI-driven fake content? With an industry specialist, the focus on identity verification is paramount for professionals across various sectors. The growing
Read more
Analyzing Voice Pitch in Vishing Attacks
Understanding the Role of Voice Frequency Analysis in Combatting Vishing Attacks How can organizations fortify their defenses against the burgeoning threat of vishing attacks, especially in mission-critical sectors? Cybersecurity professionals are increasingly turning to advanced
Read more
Real-Time Impersonation in Metaverse Meetings
By Ava Mitchell |
Deepfake & AI DetectionEnterprise Collaboration SecurityIdentity & Access Management
Is Your Organization Prepared for Metaverse Security Challenges? Where digital interactions are rapidly evolving, have you considered the implications of virtual reality on your organization’s security posture? With metaverse platforms gain traction, so do the
Read more
Deepfake Botnets: Automated Mass Impersonation
Embedding Trust in Digital Communications: A Proactive Approach to Deepfake Botnets How prepared is your organization for the inevitable advances in AI-driven threats, particularly with the rise of deepfake botnets and automated AI fraud? These
Read more
Deepfake Espionage in Industrial R&D
Understanding Threats: AI and Deepfake Technology in Corporate Espionage What happens when an impersonator can mimic your voice with chilling accuracy over a phone call or a convincing video? Welcome to the unsettling domain of
Read more
Digital Proof of Personhood
Understanding AI-Driven Threats in Identity and Access Management Is your organization prepared to counteract sophisticated AI-driven threats, particularly those utilizing deepfakes and social engineering tactics? Where digital identity trust and security have become paramount, companies
Read more
Post-Truth Cybersecurity Era
The Imperative of Real-Time Identity Verification Are we prepared to confront the sophisticated social engineering threats posed by AI-driven identity theft? With digital becomes more complex, organizations must address not just the technology behind cyber
Read more
Deepfake Legislation Guide
Understanding Deepfake Legislation How well do you truly understand the significance of deepfake legislation? With AI-driven technologies rapidly evolving, the creation of synthetic media has become more sophisticated and potentially disruptive. The challenge, therefore, is
Read more
Video-Verified Password Resets
Enhancing Security with Video Identity Verification Have you ever wondered how trust can be restored in digital interactions amidst the rise of sophisticated AI-driven threats? The continuous advance in technology has brought both incredible opportunities
Read more
Interview Deepfakes Rise
The Growing Threat of Deepfake Candidates in Hiring Processes Have you ever wondered if that candidate in the interview is truly who they claim to be? When organizations increasingly rely on digital platforms for recruitment,
Read more