Data Security & Privacy
Welcome to Impersonation Prevention Community
Main Community
Latest Posts
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security

Automated Forensic Analysis after Identity Breaches
Bridging the Gap in Digital Identity Trust: Automated Forensic Analysis after Identity Breaches How well-prepared is your organization to deal with the aftermath of identity breaches? With digital becomes increasingly complex, the threat of AI-driven
Read more
Executive Guide to Biometric Data Sovereignty
Identity Management in AI Threats Have you ever wondered how secure your organization’s identity management systems really are? While we delve into the complexities of identity verification and social engineering prevention, it’s crucial to address
Read more
Biometric Air-Gap for Executive Recovery
Enhancing Executive Security: The Role of Biometric Air-Gaps and Identity Management How can organizations tackle the sophisticated wave of AI-driven deepfake and social engineering attacks? The confluence of technology and identity verification has led to
Read more
Quantum-Resistant Identity Infrastructure
The Imperative of Identity-First Prevention Is your organization prepared to face the evolving threats posed by AI-driven deepfakes and sophisticated social engineering attacks? Where adversaries continually refine their tactics, a proactive identity-first prevention strategy is
Read more
Deepfake Audio in High-Stakes Arbitrations
Addressing the Threat of Deepfake Audio in High-Stakes Arbitrations Have you ever considered the consequences of deepfake audio in significant legal arbitrations? As a trusted AI security expert focusing on identity verification, it’s imperative to
Read more
The Rise of Digital Identity Wallets for Citizens
Addressing Security in Digital Identity Wallets What’s at stake when you can no longer differentiate between genuine and manipulated digital interactions? Digital promises unprecedented convenience, yet it also presents unique challenges, particularly in identity verification.
Read more
User-Led Identity Portability and Sovereignty
Why Is Identity Portability Essential in AI? How do we ensure that identity verification methods keep pace with the rapidly evolving capabilities of AI-driven threats? With AI technologies advance, the necessity for sophisticated identity verification
Read more
Identity Verification for High-Security R&D Staff
Enhancing Security through Advanced Identity Verification Techniques How can organizations fortify their defenses against AI-driven threats? The answer lies in adopting advanced identity verification methodologies designed to combat sophisticated attacks, particularly in mission-critical sectors. These
Read more
Quarterly Digital Footprint Audits for VIP Profiles
Why Are Quarterly Digital Footprint Audits Essential for Executives? Digital is a fast-paced and constantly evolving environment. This raises an important question: How can executives ensure their digital presence remains secure amidst escalating cyber threats?
Read more
Self-Sovereign Identity for Employee Badges
The Power of Self-Sovereign Identity in Employee Badges What makes us truly secure in our digital interactions? Where social engineering and deepfake threats are evolving at alarming rates, the concept of self-sovereign identity (SSI) becomes
Read more
Privacy Impact Assessments for Enterprise Biometrics
The Strategic Importance of Privacy Impact Assessments in Enterprise Biometrics Are organizations prepared to handle the sophisticated nature of AI-driven deception and social engineering threats? Where enterprises increasingly implement biometric solutions to enhance security, they
Read more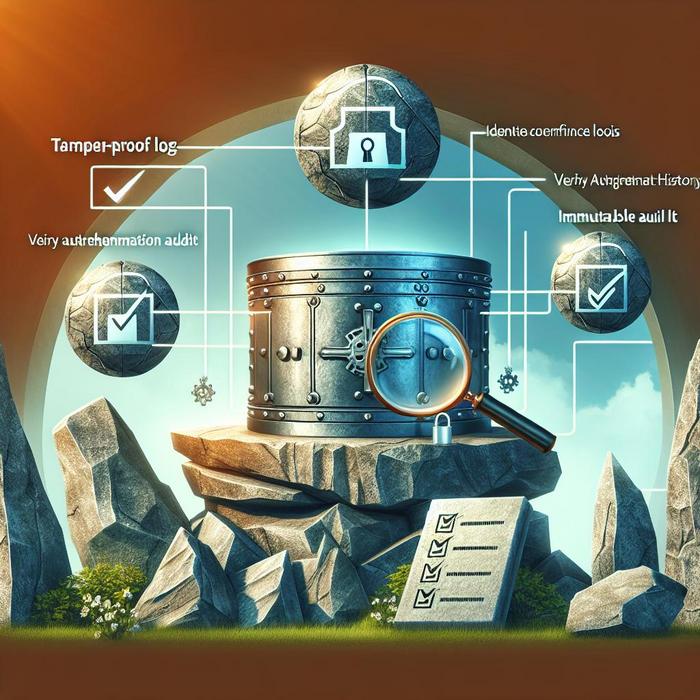
Immutable Audit Logs for Identity Events
Why Are Immutable Audit Logs Crucial for Identity Security? Have you ever wondered how your organization can effectively safeguard against AI-driven threats such as deepfake and social engineering attacks? With the surge of these digital
Read more
User-Led Biometric Data Deletion Tools
How Can Organizations Protect Against AI-Driven Deception? Digital threats has significantly evolved, and the rise of AI-powered technologies presents unique challenges for cybersecurity professionals. The emergence of AI-driven deepfakes and social engineering attacks has made
Read more
Automated Account Offboarding for Terminated Employees
Understanding the Importance of Secure Offboarding Have you ever considered the potential risks lurking behind inadequate offboarding processes? Ensuring security during employee transitions isn’t just about onboarding new talent; it’s equally crucial when it comes
Read more
Frictionless IDV for Digital Art Platforms (NFTs)
Simplicity in Identity Verification for Digital Art Platforms How can digital art platforms ensure a seamless and secure user experience while combating the increasing threats of digital fraud? With digital art becomes a frontier for
Read more
Securing the Identity of UHNW Individuals
How Secure Is the Identity of Ultra-High-Net-Worth Individuals? Digital is evolving rapidly, and with this evolution comes an increasing threat to ultra-high-net-worth individuals (UHNWI). Where the stakes are higher and the rewards for cybercriminals are
Read more
Deepfake Extortion of Public Figures’ Private Comms
How Can Organizations Protect Against Deepfake and Social Engineering Threats? Where digital communication reigns supreme, threats against organizations is increasingly dominated by sophisticated techniques such as deepfakes and social engineering attacks. With synthetic media tools
Read more