Network Security & VPN
Welcome to Impersonation Prevention Community
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security

Dynamic Identity Access Rules for Traveling VIPs
Redefining Adaptive VIP Security with Dynamic Identity Access Rules What measures are you implementing to ensure that your organization’s executive identity security is robust and adaptive? Leaders across industries are increasingly aware of the vulnerabilities
Read more
Identity Theft via Malicious Rogue Cell Towers
By Cole Matthews |
Network Security & VPNIdentity & Access ManagementEndpoint Detection & Response (EDR/XDR)
Facing the Rising Threat of Rogue Cellular Towers How do organizations stay a step ahead of cybercriminals using rogue cellular towers for identity theft? This pressing question captures the attention of IT and cybersecurity professionals.
Read more
Micro-segmentation of Identity Perimeters
The Strategic Importance of Zero Trust Identity in Combating AI-Driven Threats Is your organization equipped to handle the sophisticated AI-driven threats that lurk behind everyday digital interactions? With cyber threats continues to evolve, the importance
Read more
Identity Theft via Malicious 5G Slice Hijacking
By Madison Clarke |
Network Security & VPNIdentity & Access ManagementEndpoint Detection & Response (EDR/XDR)
Understanding the Threat of Identity Theft Through 5G Slice Hijacking How prepared is your organization for the advanced challenges posed by the latest technological advancements in mobile communication? The advent of 5G technology promises unprecedented
Read more
Moving to a Zero-Trust Identity Framework
Understanding the Rising Complexity of Identity Verification What strategies can organizations implement to protect themselves against AI-driven deepfake and social engineering attacks? With cyber threats continue to evolve, the management of identity and access management
Read more
Bypassing MFA with Real-Time Session Proxies
By Jordan Pierce |
Network Security & VPNEndpoint Detection & Response (EDR/XDR)Authentication & MFA Security
Understanding Threats MFA Proxy Attacks Are your organization’s defenses truly prepared for increasingly sophisticated multi-factor authentication (MFA) proxy attacks? A profound question, given how these threats have evolved, exploiting weaknesses in identity and access management
Read more
Conditional Access Policies for Executive VIPs
Adaptive VIP Security: Safeguarding Executive Identities How prepared is your organization to protect its most valuable assets—its executive VIPs? Where digital deception has become alarmingly sophisticated, the safeguarding of executive identities has never been more
Read more
Identity Theft via Public WiFi Spoofing
By Ava Mitchell |
Network Security & VPNIdentity & Access ManagementEndpoint Detection & Response (EDR/XDR)
Facing the Challenges of Public WiFi Security How secure do you feel when you’re using a public WiFi network at your favorite café? For many, the convenience of free internet often overshadows potential security risks.
Read more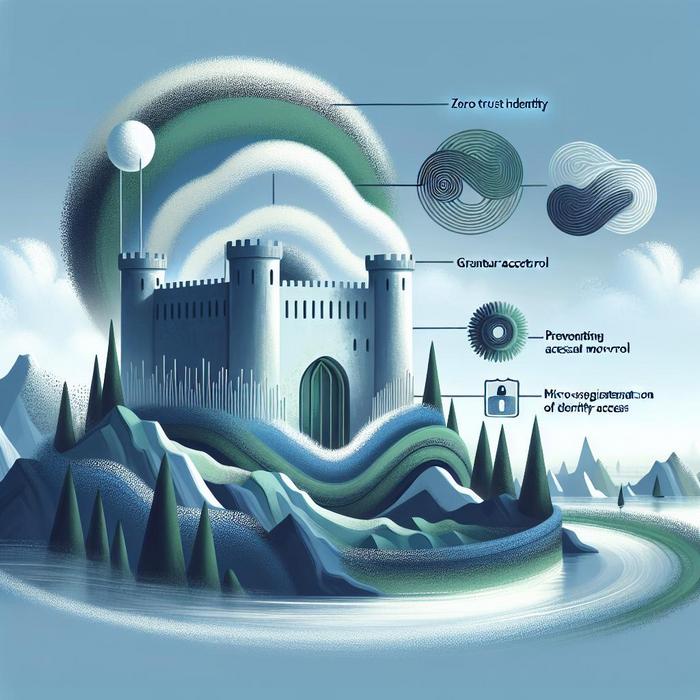
Micro-segmentation of Identity Access
Why is Achieving Zero Trust Identity Paramount for Organizations? With cyber threats increasingly leverage artificial intelligence and sophisticated tactics, organizations find themselves in a constant battle to secure their digital identities. The concept of zero
Read more
Defending Against Browser-in-the-Middle
By Madison Clarke |
Network Security & VPNEndpoint Detection & Response (EDR/XDR)Authentication & MFA Security
Understanding and Combating Advanced Browser-in-the-Middle (BitM) Threats How prepared are organizations to tackle sophisticated threats like Browser-in-the-Middle (BitM) attacks? As a pervasive form of session hijacking, these attacks manipulate user interactions with web services. They
Read more
Geofencing Executive Identities
Securing Executive Identities: A New Frontier in Identity Geofencing How do you ensure the security of high-level executives when they navigate through a digital fraught with AI-driven deception? Cybersecurity is rapidly evolving, with threats becoming
Read more
Zero Trust Identity Architecture
Understanding Zero Trust Identity Architecture How can organizations safeguard themselves against increasingly sophisticated threats? This pivotal question guides the strategic implementation of zero trust identity architecture in contemporary cybersecurity practices, reinforcing identity perimeter defenses with
Read more
Travel Security for Executives
How Secure Are Your Digital Interactions While Traveling? How often do we consider the depth of security required when executives attend international conferences or meetings? This isn’t just about safeguarding physical belongings. Digital demands a
Read more
DMARC BIMI Implementation
Enhancing Email Security with Brand Indicators: A Proactive Approach What makes a digital interaction authentic? Trust is paramount when it comes to email communication, especially when organizations are constantly under threat from AI-driven identity fraud
Read more
Email Header Analysis (DMARC)
Understanding DMARC Enforcement: A Priority for Email Security Have you ever received an email that seemed suspiciously legitimate, only to discover it was a cleverly disguised phishing attempt? This is common that highlights the critical
Read more
Mobile Deepfake Injection
By Ava Mitchell |
Network Security & VPNEndpoint Detection & Response (EDR/XDR)Deepfake & AI Detection
Securing Digital Trust in Mobile Deepfake Injection What if the very foundation of digital identity verification could be manipulated at the blink of an eye? In these sophisticated times, AI-driven threats such as mobile deepfake
Read more


