Financial & Crypto Security
Welcome to Impersonation Prevention Community
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security

Frictionless IDV for Digital Art Transactions
The Growing Importance of Identity Verification in Digital Art Transactions Have you ever questioned the authenticity of a digital artwork before making a purchase? In rapidly expanding digital art and NFTs, identity verification has become
Read more
Digital Safety for High-Net-Worth Executives
The Imperative of Proactive Identity Verification How prepared is your organization against AI-driven deepfake and social engineering threats? The stakes are higher than ever, especially for mission-critical sectors, where the consequences of a breach can
Read more
Multi-Modal Biometrics for VIP Wealth Portals
Revolutionizing Identity Security in Wealth Management with Multi-Modal Biometrics How do we secure ultra-sensitive wealth management against AI-driven threats? With digital interactions become the norm, the demand for robust identity verification systems in VIP financial
Read more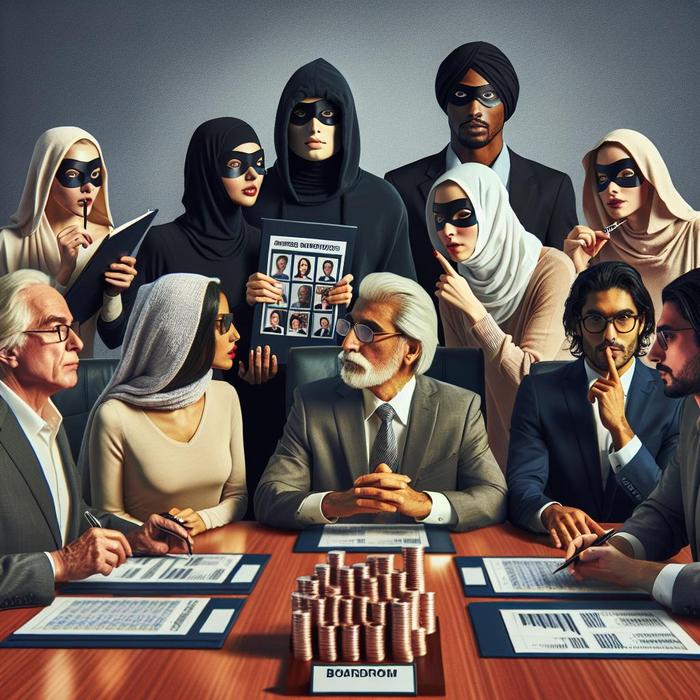
Board Member Impersonation in Hostile Takeovers
Identity Verification Strategies for Combating Boardroom Impersonation How do organizations thwart the growing threats of merger identity fraud and boardroom impersonation? Identity verification is taking center stage as a pivotal control measure. Increasingly, companies across
Read more
Unified Identity Governance for DAOs
Strengthening Identity Governance in Decentralized Autonomous Organizations How can we secure virtual lifelines against the sophisticated threats posed by AI-driven impersonators? The answer lies in a meticulous approach to identity governance, particularly pertinent for Decentralized
Read more
Zero-Knowledge Proofs in B2B Identity Portals
Guarding Digital Frontiers: Addressing AI-Driven Identity Threats What if the email you just received from a vendor is a digital forgery? Sophisticated AI-driven attacks seamlessly blend across platforms, making it challenging to discern authentic communication
Read more
Active Liveness in High-Risk Trading Sessions
Strengthening Identity Verification in High-Risk Trading Environments How secure are your high-stakes trading sessions? With digital transactions become increasingly sophisticated, so do the threats that endanger them. The core of secure trading lies in effective
Read more
Decentralized KYC for Cross-Border Logistics
Securing Global Trade through Decentralized Identity Verification How do we ensure trust in global and decentralized transactions? With international trade and finance evolves with increasing complexity, the role of decentralized know-your-customer (KYC) protocols is becoming
Read more
Low-Code Identity Verification for FinTechs
Revolutionizing Security: The Role of Low-Code Identity Verification in FinTech How secure are your existing identity verification processes where AI-driven threats continuously evolve? With digital threats become more sophisticated, organizations, especially in fintech, must enhance
Read more
Verified Credentials for Carbon Credit Markets
Digital Identity Assurance: A Guard Against Carbon Trading Fraud Have you ever wondered how secure our digital interactions are when it comes to carbon trading markets? While the drive towards sustainability is commendable, the rise
Read more
Streamlining Identity Verification for High-Stakes Finance
By Jordan Pierce |
Security Automation (SOAR)Identity & Access ManagementFinancial & Crypto Security
Strengthening Digital Defenses Against AI-Driven Threats Are your organization’s identity verification strategies keeping pace with evolving AI threats? With industries become increasingly reliant on digital platforms, the importance of securing these interactions continues to grow.
Read more
Blockchain-Verified Identity for Supply Chain Partners
By Brooke Lawson |
Third-Party & Vendor SecurityIdentity & Access ManagementFinancial & Crypto Security
The Growing Complexity of AI-Driven Social Engineering in Supply Chains Have you ever pondered the intricate maze of digital interactions that occur every second in global supply chains? I’m acutely aware that the sophistication of
Read more
Balancing Identity Security and UX in Retail Banking
Are Retail Banks Making the Right Trade-off Between Identity Security and Customer Experience? Technology is evolving at an unprecedented rate, and retail banks face the twin challenges of ensuring robust identity verification (IDV) against sophisticated
Read more
Decentralized Multi-factor Authentication (dMFA)
By Dylan Keane |
Identity & Access ManagementFinancial & Crypto SecurityAuthentication & MFA Security
Strengthening Security: The Imperative of Decentralized Multi-factor Authentication Have you ever wondered how easily your digital identity could be compromised by advanced AI attacks? This looming question is at the heart of cybersecurity concerns as
Read more
Deepfake Disruption of Real-Time Stock Earnings Calls
The Rise of Synthetic Earnings Calls: A New Threat to Investors Have you ever wondered how secure our financial communications truly are? Imagine listening to a corporate earnings call, confident in insights provided by the
Read more