Identity Fraud Prevention
Welcome to Impersonation Prevention Community
Main Community
Latest Posts
Latest Posts
- AI-driven Cybersecurity
- Application & Code Security
- Authentication & MFA Security
- Cloud Security
- Compliance & Reporting
- Critical Infrastructure Security
- Data Security & Privacy
- Deepfake & AI Detection
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Enterprise Collaboration Security
- Enterprise Cybersecurity
- Executive & VIP Protection
- Financial & Crypto Security
- Healthcare Security
- Hiring & Onboarding Security
- Identity & Access Management
- Identity Fraud Prevention
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- Remote Work Security
- Security Automation (SOAR)
- Security Awareness & Training
- Social Engineering Prevention
- Third-Party & Vendor Security
- Threat Intelligence
- Threat Intelligence & Prevention
- Vulnerability & Risk Management

Passkeys & Passwordless Adoption
Addressing the Emerging Threat of AI-Driven Deception Can your organization distinguish a legitimate communication from a sophisticated scam? The fusion of artificial intelligence with social engineering techniques is leading to an unprecedented rise in deepfake
Read more
Document Liveness Detection
Understanding the Challenges of ID Document Liveness Detection How secure are your current identity verification measures? With the accelerated pace of technology, cyber adversaries are deploying increasingly sophisticated AI-driven threats, leading to a pressing need
Read more
Synthetic Identity Fraud
The Rise of Synthetic Identity Fraud What makes synthetic identity fraud an inevitable threat? With cybercriminals continuously adapt in sophistication, organizations find themselves on the defensive against increasingly complex threats. Among the most insidious of
Read more
Prevent account takeover deepfake
Why Are Organizations Focusing Intensely on ATO Prevention? With cyber threats evolve, businesses are battling the tidal wave of account takeover (ATO) incidents, particularly those powered by sophisticated deepfake technologies. The question is, how can
Read more
Prevent deepfake job applicants
The Growing Threat of Deepfake Job Applicants Have you ever wondered how deeply fake technologies are woven into the fabric of contemporary digital threats? While advancements in artificial intelligence continue to redefine cyber, we find
Read more
Verify Identity of Candidates
The Rising Complexity of Identity Verification Have you ever wondered how secure your organization’s candidate identity check processes are where dominated by artificial intelligence and digital deception? When organizations increasingly rely on advanced technologies for
Read more
Deepfake Detection Tools
Evolving Threats Deepfake Technology What makes the combat against deepfakes more pressing than ever? With technology advances, so do the methods and sophistication of cyber threats. Among the most worrying are AI-driven deepfake and social
Read more
Secure Hiring
Emerging Threats in Identity Verification During Hiring Processes Are your organization’s hiring procedures resilient enough to combat AI-driven deception? With the increasing prevalence of AI-driven identity spoofing techniques such as deepfakes, organizations must rethink how
Read more
Identity Verification (IDV)
Digital Identity Verification: A Strategic Imperative for Cybersecurity Have you ever wondered how to maintain trust in digital communications when threats like deepfake and AI-driven social engineering attacks are becoming increasingly sophisticated? This question is
Read more
AI Deepfake fraud
The Strategic Role of Identity Verification in Preventing AI-Driven Deception How can organizations safeguard themselves from the sophisticated deception posed by AI-driven deepfake and social engineering attacks? Where artificial intelligence technologies evolve rapidly, security professionals
Read more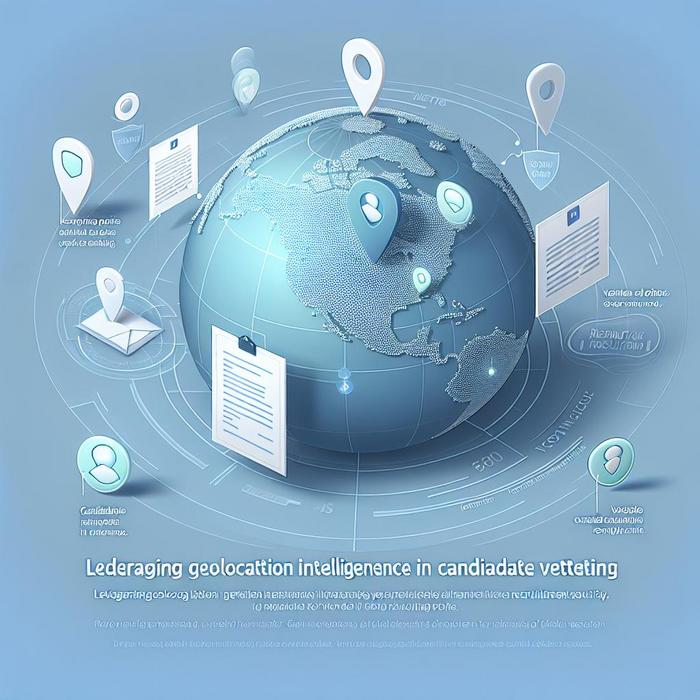
Leveraging Geolocation Intelligence in Candidate Vetting
How Geolocation Intelligence Transforms Candidate Vetting Is your organization equipped to deal with evolving recruitment security and candidate location fraud? The impact of technology introduces both opportunities and challenges. With AI and advances in data
Read more
Monitoring for Mouse Jiggling Software on Laptops
By Kelsey Jones |
Endpoint Detection & Response (EDR/XDR)Identity Fraud PreventionRemote Work Security
Understanding the Risks of Mouse Jiggling Software in Remote Work Environments Are your organization’s security measures robust enough to tackle the sophisticated challenges posed by AI-driven threats? Where remote work has become a staple, safeguarding
Read more
Verify Phone Numbers to Spot VoIP Recruitment Fraud
Unmasking VoIP Recruitment Fraud: A Critical Challenge for Cybersecurity Experts Have you ever wondered how perilous it is when identity verification measures fall short? Where sophisticated AI-driven deepfake and social engineering attacks are on the
Read more
Spotting AI-Generated Profile Pictures in Vetting
Understanding AI-Driven Threats in Identity Verification How can organizations fortify their defenses against the growing wave of AI-driven identity threats? The rapid advancement of artificial intelligence has ushered where deception is becoming increasingly sophisticated. Deepfake
Read more