Identity Fraud Prevention
Welcome to Impersonation Prevention Community
Latest Posts
- AI-driven Cybersecurity
- Application & Code Security
- Authentication & MFA Security
- Cloud Security
- Compliance & Reporting
- Critical Infrastructure Security
- Data Security & Privacy
- Deepfake & AI Detection
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Enterprise Collaboration Security
- Enterprise Cybersecurity
- Executive & VIP Protection
- Financial & Crypto Security
- Healthcare Security
- Hiring & Onboarding Security
- Identity & Access Management
- Identity Fraud Prevention
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- Remote Work Security
- Security Automation (SOAR)
- Security Awareness & Training
- Social Engineering Prevention
- Third-Party & Vendor Security
- Threat Intelligence
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
Background Check Spoofing
Understanding the Risks of Fake Background Results What happens when your meticulously crafted security protocols are rendered useless by a single identity verification failure? With technology progresses, so do the threats associated with it. The
Read more
Interview Deepfakes Rise
The Growing Threat of Deepfake Candidates in Hiring Processes Have you ever wondered if that candidate in the interview is truly who they claim to be? When organizations increasingly rely on digital platforms for recruitment,
Read more
Detecting AI-Generated IDs
Why is Identity Verification Crucial in Digital? Identity verification has become a cornerstone of cybersecurity. It’s not just about keeping the wrong people out; it’s about maintaining the integrity and trustworthiness of our digital communities.
Read more
The Evolution of Generative Identity
Understanding the Risks of Generative Identity and AI Persona Creation What makes the combination of generative AI and identity so potent? The advent of sophisticated AI technologies has brought not only opportunities but also significant
Read more
Real-time Deepfake Stream Hijacking
By Jordan Pierce |
Deepfake & AI DetectionEnterprise Collaboration SecurityIdentity Fraud Prevention
Understanding Threats Real-Time Deepfake Attacks Have you ever questioned the authenticity of a video message you received? It is crucial to understand how real-time deepfake stream hijacking can affect an organization. This growing menace exploits
Read more
Medical Identity Theft
Understanding the Threat of Medical Identity Theft What are the implications of medical identity theft where digital threats are increasingly sophisticated? This question should resonate with industry professionals who face the challenge of securing sensitive
Read more
Dark Web Identity Monitoring
Identity Verification in AI-Veiled Attacks What actions are organizations taking to safeguard their digital interactions? With digital expands, so too does the potential for AI-driven threats. The sophistication of these threats, from social engineering attacks
Read more
Account Recovery Fraud
The Growing Menace of Account Recovery Scams Have you ever considered how easily access to sensitive information could be compromised, despite robust security measures? While we delve into the complexities of digital identity verification, the
Read more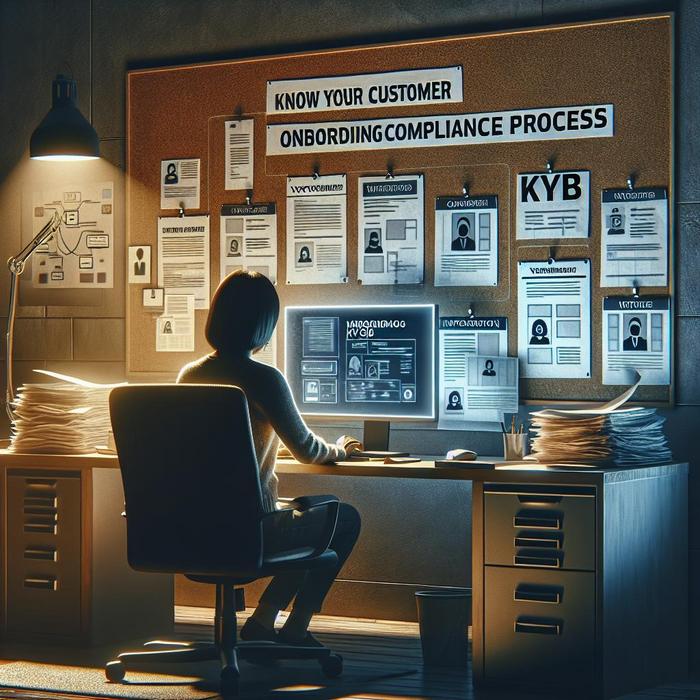
KYC KYB Process Security
Understanding Risk: Safeguarding KYC and KYB Processes What measures are you taking to secure your organization’s identity verification processes? Threats has expanded, bringing new challenges to Know Your Customer (KYC) and Know Your Business (KYB)
Read more
Live Face Swap Attacks
Understanding the Risks of Live Deepfake Attacks Are you fully prepared to defend against the latest wave of cyber threats? AI advances have amplified the sophistication of cyber-attacks, with live deepfake attacks or face swaps
Read more
Voice Cloning in Call Centers
Understanding Threats in Modern Call Centers How secure is your call center against the advent of voice cloning and AI-driven attacks? The sophistication of AI technologies has brought both innovation and a formidable new range
Read more
Ghost Employees & Payroll Fraud
The Undetected Threat: Ghost Employees & Payroll Fraud How often do we consider the threats lurking silently? Ghost employees and payroll fraud are among the clandestine tactics that can financially cripple organizations, leaving decision-makers in
Read more