Identity Fraud Prevention
Welcome to Impersonation Prevention Community
Latest Posts
- AI-driven Cybersecurity
- Application & Code Security
- Authentication & MFA Security
- Cloud Security
- Compliance & Reporting
- Critical Infrastructure Security
- Data Security & Privacy
- Deepfake & AI Detection
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Enterprise Collaboration Security
- Enterprise Cybersecurity
- Executive & VIP Protection
- Financial & Crypto Security
- Healthcare Security
- Hiring & Onboarding Security
- Identity & Access Management
- Identity Fraud Prevention
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- Remote Work Security
- Security Automation (SOAR)
- Security Awareness & Training
- Social Engineering Prevention
- Third-Party & Vendor Security
- Threat Intelligence
- Threat Intelligence & Prevention
- Vulnerability & Risk Management

Vulnerability of Mobile Recovery Emails
By Madison Clarke |
Authentication & MFA SecurityEndpoint Detection & Response (EDR/XDR)Identity Fraud Prevention
Navigating the Complexities of Mobile Identity Risks Have you considered the hidden dangers lurking within your mobile recovery emails? The security of our mobile identities has become paramount. Organizations, especially those in mission-critical sectors, are
Read more
The Risk of Identity Re-use across SaaS
The Growing Threat of Identity Reuse in SaaS Environments Have you ever wondered how secure your digital identity is across multiple platforms? With the rise of Software as a Service (SaaS), the potential for identity
Read more
Securing Instant Payment Identities (FedNow Zelle)
Complex Instant Payment Fraud How can organizations protect themselves against the sophisticated threats of real-time transfer security breaches? The advent of systems like FedNow and Zelle has revolutionized financial transactions, allowing money to flow almost
Read more
Real-Time Forensic ID Document Analysis
Transforming Identity Verification: Ensuring Trust What steps are your organization taking to safeguard its identity verification processes against sophisticated AI threats? Where the line between reality and deception blurs with the rise of deepfake technology,
Read more
Identity Theft as a Commodity
The Growing Challenge of AI-Driven Identity Verification Have you ever considered how AI-driven identity threats can immobilize critical sectors? When organizations strive to safeguard digital identity trust, the increasing sophistication of AI-driven social engineering and
Read more
AI-Driven Identity Risk Scoring
The Importance of Proactive Measures in AI-Driven Identity Security How does your organization protect itself where cyber threats increasingly exploit AI technologies? Digital security is evolving faster than ever, demanding foresight and adaptability. Understanding the
Read more
The Fragility of Knowledge-Based Auth (KBA)
By Brooke Lawson |
Authentication & MFA SecurityIdentity & Access ManagementIdentity Fraud Prevention
Understanding the Limitations of Knowledge-Based Authentication Have you ever questioned the reliability of the security methods protecting your organization? The limitations of traditional security measures, such as Knowledge-Based Authentication (KBA), have become glaringly apparent. While
Read more
Protecting Against Real-Time Account Porting
By Cole Matthews |
Authentication & MFA SecurityFinancial & Crypto SecurityIdentity Fraud Prevention
Proactive Measures to Combat Account Porting Threats Have you ever questioned the integrity of your organization’s communication channels and wondered if they’re susceptible to AI-driven manipulation? This is a prevalent concern among many cybersecurity professionals,
Read more
The Industrialization of Identity Theft
Understanding the Unseen Threat: Mass Identity Fraud in AI Have you considered how mass identity fraud is evolving ? With digital interactions become increasingly woven into the fabric of our daily lives, threats has radically
Read more
Account Hijacking via Port-Out Scams
By Ava Mitchell |
Authentication & MFA SecurityEndpoint Detection & Response (EDR/XDR)Identity Fraud Prevention
Understanding the Growing Threat of Account Hijacking through Port-Out Scams How secure are your digital interactions? This question haunts many organizations, especially those in mission-critical sectors. With cybercriminals become increasingly sophisticated, threats has expanded, including
Read more
Hostile Takeover via Identity Manipulation
Understanding and Countering the Threat of Identity Manipulation What happens when the very channels meant to protect us become tools in cybercriminals? Identity manipulation poses a significant threat to organizations, particularly those within mission-critical sectors.
Read more
Combating False Positives in Fraud Detection
By Brooke Lawson |
Identity Fraud PreventionSecurity Automation (SOAR)Vulnerability & Risk Management
Enhancing Fraud Detection Accuracy Amidst AI-Driven Threats What measures can organizations take to protect themselves with AI-powered threats become more sophisticated? The assault on digital trust is intensifying, with AI and machine learning technologies enabling
Read more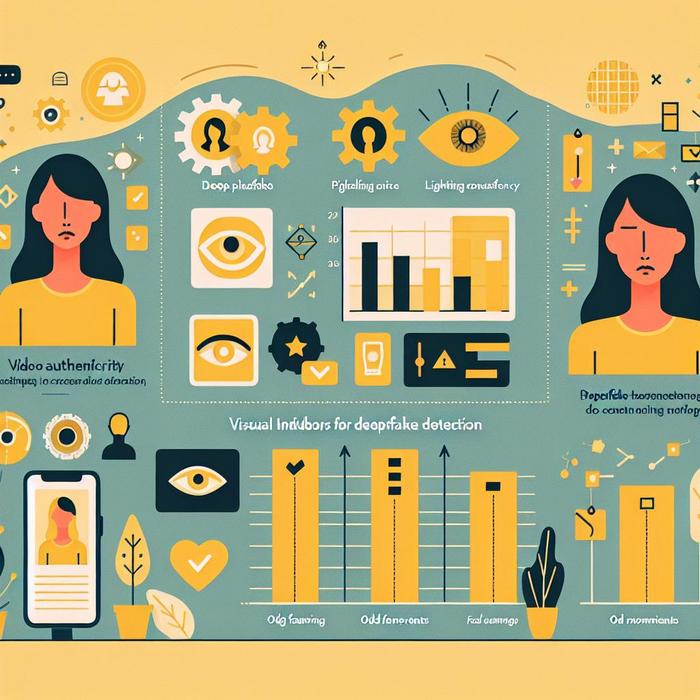
Visual Indicators for Deepfake Detection
Understanding AI-Driven Identity Threats How can organizations effectively combat the sophisticated threats posed by AI-driven fake content? With an industry specialist, the focus on identity verification is paramount for professionals across various sectors. The growing
Read more
Ghosting & Identity Theft in Gig Platforms
The Gig Economy’s Hidden Threat: Identity Theft and Ghosting Have you ever wondered how secure your identity is? With digital platforms like Uber, Fiverr, and others become integral to our daily lives, they also open
Read more
Automating Identity Risk
Enhancing Security with Risk-Based Identity Solutions How can organizations effectively mitigate the sophisticated threats posed by AI-driven attacks? This question is at the forefront for many industry leaders and security professionals. With cybercriminals become more
Read more
Financial ATO Prevention
Confronting the Threat: AI-Driven Identity Security in Financial Services Are you confident that your financial institution’s defenses are equipped to handle the sophisticated threats posed by AI-driven deepfake and social engineering attacks? Safeguarding against these
Read more
Patient Impersonation Telehealth
Understanding Medical Identity Fraud in Telehealth Have you ever considered the risk of medical identity fraud in telehealth settings? While the healthcare industry embraces digital transformation, driven by the necessity for remote consultations, there’s an
Read more