Welcome to Impersonation Prevention Community
Redefining Digital Trust in the GenAI Era
The Impersonation Prevention Community unites security leaders to combat deepfakes and social engineering in the GenAI era. We invite CISOs, risk officers, and experts to share insights on identity first telemetry driven verification using device fingerprinting, network signals, and digital IDs to stop impersonation at its source and restore digital trust.
Latest Posts
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security

Identity Theft via Malicious Rogue Cell Towers
By Cole Matthews |
Network Security & VPNIdentity & Access ManagementEndpoint Detection & Response (EDR/XDR)
Facing the Rising Threat of Rogue Cellular Towers How do organizations stay a step ahead of cybercriminals using rogue cellular towers for identity theft? This pressing question captures the attention of IT and cybersecurity professionals.
Read more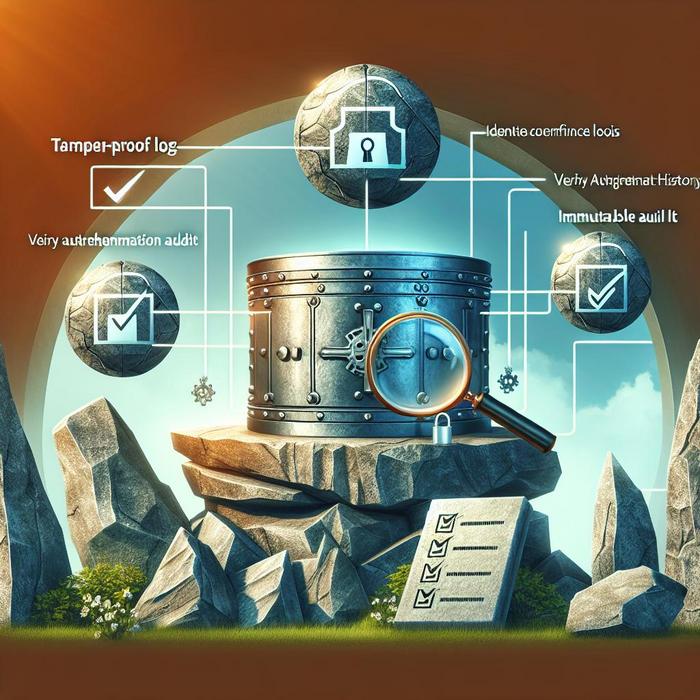
Immutable Audit Logs for Identity Events
Why Are Immutable Audit Logs Crucial for Identity Security? Have you ever wondered how your organization can effectively safeguard against AI-driven threats such as deepfake and social engineering attacks? With the surge of these digital
Read more
MFA Enforcement for Third-Party Management Portals
By Cole Matthews |
Third-Party & Vendor SecurityIdentity & Access ManagementAuthentication & MFA Security
Strengthening Third-Party Security: MFA Enforcement in Management Portals How prepared is your organization? This is a crucial question for those in cybersecurity, particularly when it comes to securing third-party management portals. Multi-factor authentication (MFA) is
Read more
Multi-Modal Biometrics for High-Sec Remote Access
Why Are Multi-Modal Biometrics Essential for High-Security Remote Access? Where threats like AI-driven deepfakes and social engineering attacks are becoming increasingly sophisticated, how do organizations ensure that digital identities are secure? The answer lies in
Read more
Fake IT System Update Alerts via Push Notification
By Kelsey Jones |
Malware & Botnet SecurityIT & Help Desk SecurityEndpoint Detection & Response (EDR/XDR)
Understanding Threats Malicious Updates How do organizations safeguard their IT infrastructure against deceptive tactics like fake system update alerts? This question is increasingly critical for businesses across sectors, especially with sophisticated cyber threats evolve. One
Read more
User-Led Biometric Data Deletion Tools
How Can Organizations Protect Against AI-Driven Deception? Digital threats has significantly evolved, and the rise of AI-powered technologies presents unique challenges for cybersecurity professionals. The emergence of AI-driven deepfakes and social engineering attacks has made
Read more
Deepfake Sabotage of Company Earnings Forecasts
Combating Financial Deepfake Attacks on Earnings Forecasts Is your organization equipped to handle the mounting threat of financial deepfake attacks? The rise of sophisticated AI-driven attacks presents a profound challenge for organizations across sectors. Deepfake
Read more
The Evolution of Identity Fraud Markets
Understanding Identity Fraud Could your organization fall prey to mass identity fraud? While we delve into evolving digital security, one cannot ignore the growing sophistication of identity fraud markets. Where every click, chat, and transaction
Read more
Protecting Help Desk from AI-generated Video IDV
Understanding AI-Driven Threats in Identity Verification How can organizations shield themselves from increasingly sophisticated AI-generated video fraud? With technology evolves, so too do the methods of cybercriminals. Attackers employ advanced techniques like deepfake videos to
Read more
Identity Governance for High-Turnover Seasonal Staff
Addressing the Challenges of Identity Governance for High-Turnover Seasonal Staff What makes the modern workforce so susceptible to AI-driven deception? With the advent of sophisticated AI tools and increasingly lifelike deepfakes, organizations are facing unprecedented
Read moreContent on the Impersonation Prevention Community is created by guest contributors and is provided as community-generated material, not official company communication or endorsement. While we attempt to review submissions, we do not guarantee their accuracy and are not responsible for the opinions expressed. Readers should independently verify all information.