Threat Intelligence
Welcome to Impersonation Prevention Community
Latest Posts
- Security Awareness & Training
- Executive & VIP Protection
- Authentication & MFA Security
- Compliance & Reporting
- Data Security & Privacy
- Email Security & Anti-Phishing
- Email Security & Anti-Spam
- Endpoint Detection & Response (EDR/XDR)
- Application & Code Security
- Financial & Crypto Security
- Identity & Access Management
- IT & Help Desk Security
- Malware & Botnet Security
- Network Optimization
- Network Security & VPN
- Ransomware & Backup Security
- AI-driven Cybersecurity
- Third-Party & Vendor Security
- Threat Intelligence & Prevention
- Vulnerability & Risk Management
- Hiring & Onboarding Security
- Threat Intelligence
- Social Engineering Prevention
- Security Automation (SOAR)
- Remote Work Security
- Identity Fraud Prevention
- Healthcare Security
- Enterprise Cybersecurity
- Enterprise Collaboration Security
- Deepfake & AI Detection
- Critical Infrastructure Security
- Cloud Security

Threat Hunting for Executive Look-alike Profiles
Innovative Strategies to Combat Executive Impersonation How secure is your organization against the evolving threat of executive impersonation? The sophistication of cybercriminals has escalated dramatically, leveraging artificial intelligence to craft deepfake profiles and perpetrate social
Read more
Impersonating Flash Loan Arbitrageurs in DeFi
Understanding the Gravity of DeFi Fraud and Flash Loan Scams What measures can organizations take to fortify their defenses against AI-driven identity security threats? With technology evolves, cyber threats becomes increasingly complex, particularly in decentralized
Read more
Automated Domain Name Dispute Resolution (UDRP)
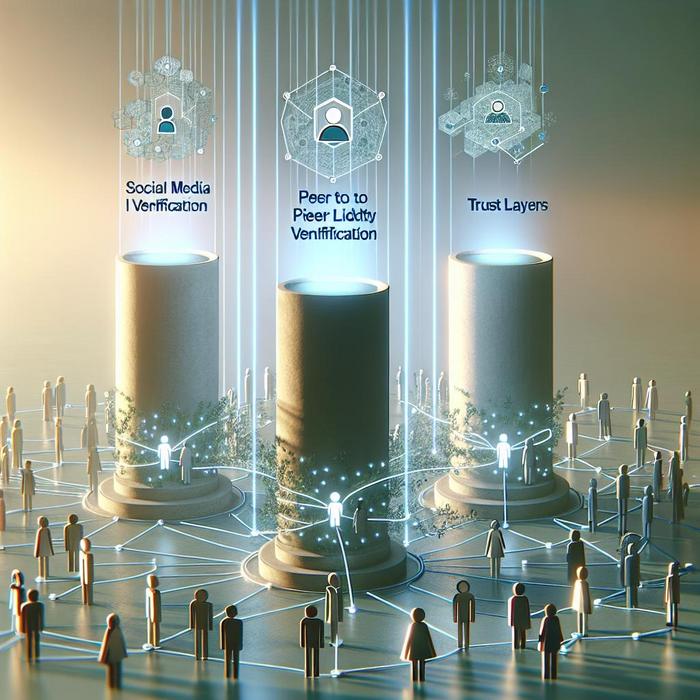
The Critical Role of Identity Verification in Combating AI-Driven Threats Have you ever wondered how secure your organization’s digital interactions truly are? Where attackers leverage AI to craft sophisticated deceptions, identity verification stands as a
Read more
Threat Hunting for Executive Digital Shadows
Understanding the Executive Digital Footprint Have you ever considered how executives’ digital presence can inadvertently expose vulnerabilities to cyber threats? The executive digital footprint refers to the online presence of high-level executives, encompassing everything from
Read more
Impersonating Open Source Maintainers
Transforming Identity Verification Systems to Combat AI-Driven Threats How can your organization ensure the integrity of digital interactions, AI-driven identity fraud and social engineering? With cybercriminals become more sophisticated, leveraging AI to create convincing deepfakes
Read more
Deepfake Ransomware Negotiations
Understanding the Threat of AI-Driven Social Engineering Are organizations prepared to combat the growing threat of fake ransom negotiators and synthetic extortion? The rise of artificial intelligence (AI) has revolutionized industries, but it has also
Read more
Abusing Webhooks for Identity Injection
Understanding the Threat of Webhook Security Have you ever thought about the potential risks lurking in connections your organization relies on for seamless digital operations? Webhooks, a modern linchpin for automated data exchanges, are highly
Read more
The Role of AI in Scaling Brand Protection
Why Is Scaling Takedowns Crucial for Brand Safety? Where technology is rapidly advancing, and artificial intelligence (AI) plays a pivotal role, protecting brand integrity is more essential than ever. With digital platforms grow, so does
Read more