TL;DR/ Executive Summary
| Threat | DPRK-affiliated IT workers applying for remote technical roles at a global enterprise |
| Detection window | Pre-employment screening, Q1 2026 |
| Flagged | 4 candidates exhibiting high-confidence DPRK IT worker indicators |
| TTPs observed | Proxy, Multi-hop proxy, Remote access software, Account establishment |
| Tools Used | Astrill VPN, AnyDesk, ThisaProxy, HostPapa infrastructure, CyberGhost VPN, Urban VPN, VoIP number provisioning |
| Attribution Confidence | Moderate-to-high; based on TTP alignment with published DPRK IT worker tradecraft |
| MITRE ATT&CK | T1090 · T1090.003 · T1219 · T1585 · |
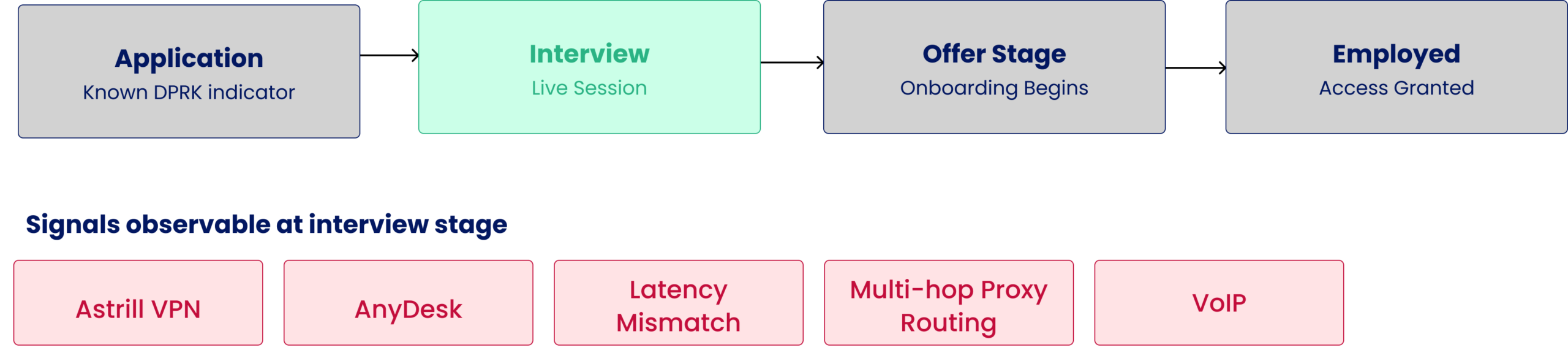
During pre-employment verification of 600 candidates, imper.ai identified four individuals exhibiting device, network, and identity signals consistent with the Democratic People’s Republic of Korea (DPRK) IT worker tradecraft, as documented across multiple independent threat intelligence sources. Each candidate presented overlapping indicators: Astrill VPN usage, layered proxy routing, AnyDesk usage, inconsistent geographic latency with a claimed US location, VoIP phone numbers, and newly created or low-activity email accounts.
This brief documents the observed indicators, maps them to published tradecraft, and provides detection guidance for security teams responsible for protecting the hiring pipeline.
Threat Actor Background
Since at least 2022, the Democratic People’s Republic of Korea has operated structured programs deploying IT workers globally to generate hard currency for the regime — revenue assessed to support sanctions evasion and WMD programs. These workers pose as non-North Korean nationals and apply for remote technical positions, primarily targeting US-based companies.
The scale is significant. According to US Department of Justice findings cited in Unit 42’s research¹, individual IT workers can earn up to $300,000 annually, with the North Korean government retaining up to 90% of those earnings, generating hundreds of millions of dollars per year collectively.
This activity is tracked under multiple aliases across vendors: Wagemole (Unit 42 / Palo Alto Networks), UNC5267 (Google Mandiant), Nickel Tapestry / Jasper Sleet (Microsoft), and is a component of the broader Contagious Interview campaign cluster tracked by GitLab² and others. Workers operate primarily out of China and Russia, with smaller populations in Africa and Southeast Asia, using controlled infrastructure to project a US-based identity.
The threat is not theoretical. In June 2025, Microsoft published research on Jasper Sleet documenting active infiltration attempts across enterprises. In February 2026, GitLab’s threat intelligence team identified and banned accounts used in active Contagious Interview and IT worker operations, finding that some private repositories contained malware artifacts and records directly supporting IT worker activity and sanctions evasion. The TTP set has remained consistent across this entire period.
Observed TTPs
The following indicators were observed across the four flagged candidates. Each TTP is documented in the referenced published research; imper.ai’s findings represent independent corroboration of a well-established pattern.
Astrill VPN — T1090 & T1090.003 (Multi-hop)
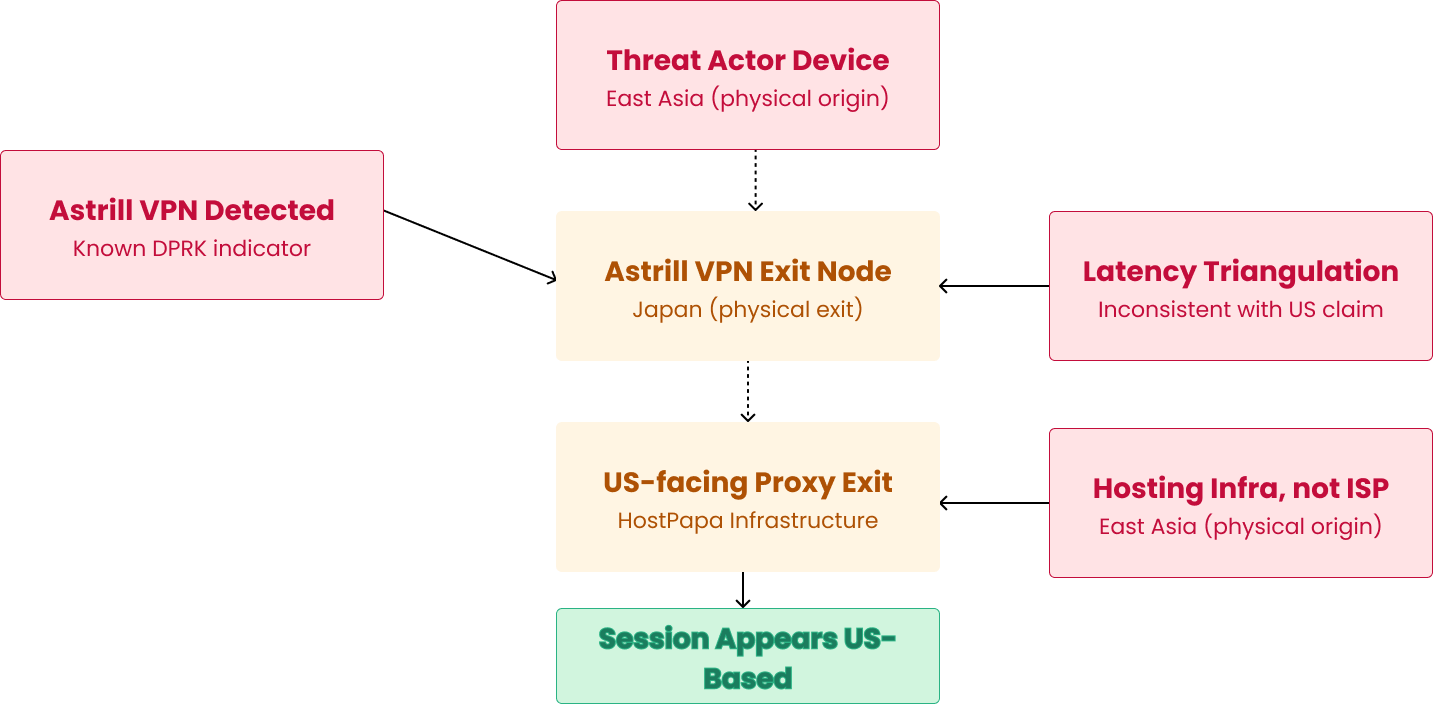
Astrill VPN was detected across multiple candidates, in one case as part of a multi-hop chain: traffic routed through Astrill into a Japan exit node, then forwarded to a US-facing proxy to present a US-origin session. See below for further details on multi-hop proxy usage and latency mismatch.
Astrill VPN is not a generic commercial VPN. Its consistent, specific appearance across DPRK IT worker investigations by independent research teams makes it a high-confidence discriminating indicator in this context — not merely a privacy tool used by a privacy-conscious candidate. Spur.us released a public blocklist of approximately 2,400 active Astrill VPN exit IPs in December 2024, specifically in response to its documented use in this threat cluster. GitLab’s February 2026 report identifies Astrill as consistent infrastructure across both Contagious Interview and IT worker campaigns.
AnyDesk — T1219 (Remote Access Software)
AnyDesk was installed and detected on two candidates’ devices. In the context of a live interview for a technical role, this indicator carries specific operational significance: it is consistent with a third party remotely controlling the candidate’s device in real time — either to assist with or fully conduct technical assessments on the candidate’s behalf.
This technique, using remote desktop tools to facilitate impersonation during interviews, is well-documented. Having AnyDesk installed in isolation is not determinative, but in combination with Astrill VPN, VoIP artifacts, and latency inconsistencies, it materially elevates the risk profile.
VoIP / Virtual Phone Numbers
VoIP numbers were associated with all four flagged candidates. VoIP numbers are provisioned programmatically, carry no verifiable residential footprint, and are trivially obtained at scale. Combined with a newly registered or low-activity email account, this profile describes a purpose-built synthetic identity constructed for a specific application — not a genuine individual with an established digital presence.
Unit 42’s Wagemole research and Google Mandiant’s UNC5267 documentation both call out VoIP-based fabrication as a consistent component of DPRK IT worker persona construction.
Layered Proxy Routing and Latency Mismatch — T1090
Two distinct sub-patterns were observed:
- Multi-layer VPN stacking: One candidate had Astrill VPN active at the OS level and CyberGhost and Urban VPN installed as browser extensions — three distinct VPN providers. Multi-provider VPN stacking of this type is not associated with any legitimate candidate use case. It is operationally consistent with belt-and-suspenders anonymization: if one layer fails or is detected, the next provides continued obfuscation.
- Geographic latency mismatch: Multiple candidates configured US-based timezone settings while exhibiting network latency inconsistent with US geographic presence. In one case, BGP-level network proximity analysis indicated strong East Asian origin despite a US-facing session. Timezone configuration is trivially manipulated; latency is a physical property and cannot be fully spoofed. The delta between configured location and measured latency is a non-spoofable signal.
Low-Trust Identity Artifacts — T1585
Across all four candidates: low-activity Gmail accounts combined with VoIP phone numbers. This identity profile — no account tenure, no verifiable history, virtual phone number — is consistent with purpose-built personas. Google Mandiant’s UNC5267 research documents similar patterns, including fabricated resume pages with mismatched identity details across documents and stolen profile images from LinkedIn.
TTP Summary
| TTP | MITRE | Signal | Corroborating sources |
| Astrill VPN | T1090.003 | OS-level VPN; multi-hop proxy | GitLab, Recorded Future, Microsoft, Mandiant, Team Cymru, Spur.us |
| AnyDesk | T1219 | Remote access tool on interview device | Recorded Future, Microsoft, Mandiant, Team Cymru, any.run |
| VoIP phone numbers | T1586 | Virtual numbers on all four candidates | Unit 42, Mandiant |
| Layered proxy / latency mismatch | T1090 | VPN stack; East Asian latency vs. US session | GitLab, Recorded Future, Spur.us |
| Low-trust identity artifacts | T1585 | Low activity email account history | Mandiant/UNC5267 |
Case Observations
The four candidates below were flagged during pre-employment verification for technical roles. Signal assessments are based on device, network, and identity data captured at the time of screening. No single indicator is treated as determinative; assessments reflect the combination of signals present.
Candidate A — Multi-hop Proxy with East Asian Network Origin
Network signals:
- Session presented as US-origin; underlying analysis revealed HostPapa hosting infrastructure rather than a residential ISP — consistent with use of a rented exit node
- Multi-hop proxy chain: Astrill VPN → Japan exit node → US-facing proxy
- BGP-level network proximity analysis: strong East Asian origin, irreconcilable with genuine US presence
Identity signals:
- VoIP phone number
Assessment: High confidence. The routing topology is not consistent with any legitimate candidate behavior. Multi-hop VPN chaining through Japan to a US proxy exit, combined with hosting-associated infrastructure, represents deliberate operational tradecraft for location obfuscation. The East Asian network origin indicated by proximity analysis is consistent with the primary operating locations of DPRK IT workers documented in published intelligence.
Candidate B — Remote Access Tool and Environmental Manipulation
Network signals:
- Astrill VPN active
- US timezone configured; measured latency irreconcilable with US presence
Device signals:
- AnyDesk detected
Identity signals:
- Inactive Gmail account
- VoIP phone number
Assessment: High confidence. The presence of AnyDesk software, combined with Astrill VPN and a latency/location mismatch, is consistent with live impersonation via remote desktop control. The inactive Gmail account and VoIP number indicate a low-trust synthetic identity.
Candidate C — Multi-layer Anonymization Stack
Network signals:
- Astrill VPN active at OS level
- CyberGhost VPN and Urban VPN detected as active browser extensions
- High latency inconsistent with US presence
Identity signals:
- Inactive email account
- VoIP phone number
Assessment: High confidence. The concurrent use of three VPN providers — OS-level plus two browser extensions — is strongly atypical and operationally consistent with layered anonymization infrastructure. Signal profile is substantially similar to Candidate B. The appearance of four candidates with overlapping TTP signatures within the same hiring cohort, regardless of interview scheduling, constitutes a non-trivial concentration of risk and warrants escalation.
Candidate D — Remote Access and Layered Anonymization Profile
Network signals:
- Astrill VPN active
- High latency inconsistent with US presence — network measurements indicate operation from outside the US despite a US-configured session
Device signals:
- AnyDesk detected
Identity signals:
- Two phone numbers on file — both VoIP — no verified real-world identity anchor
- Inactive Google account — lacking the account history expected of a genuine candidate
Assessment: High confidence. Candidate D presents a near-identical signal profile to Candidate B: Astrill VPN, AnyDesk, latency irreconcilable with US presence, and a low-trust synthetic identity. The presence of two distinct VoIP numbers rather than one is operationally notable — it is consistent with maintaining multiple contact points across persona sets, a pattern documented in DPRK IT worker research. The inactive Google account further erodes the legitimacy of the candidate’s stated identity. The appearance of this profile as a fourth independent instance within the same hiring cohort significantly elevates the collective attribution confidence beyond what any single candidate would support in isolation.
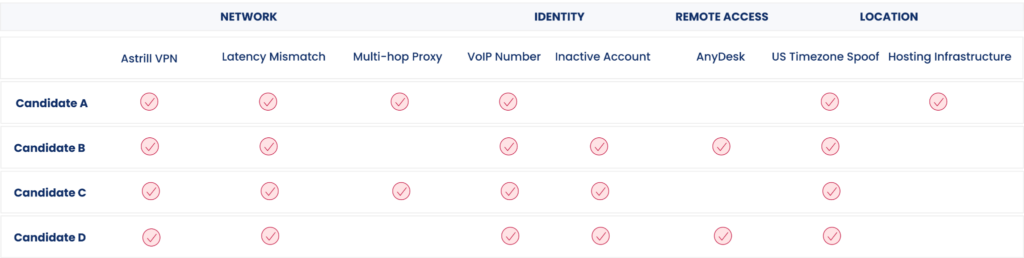
Assessment
The four flagged candidates each independently present a signal combination consistent with documented DPRK IT worker tradecraft. The evidential weight is not in any individual indicator — Astrill VPN usage alone, or a VoIP number alone, would not be sufficient — but in the co-occurrence of network, device, and identity signals that collectively describe operational infrastructure rather than a legitimate candidate environment.
Astrill VPN is the strongest discriminating indicator in this set. Its repeated, specific documentation across independent research teams investigating the same threat cluster — from Mandiant’s 2022–2024 UNC5267 work through GitLab’s February 2026 report — places it in a different category from generic VPN usage. A candidate using Astrill VPN in combination with AnyDesk and a VoIP-based telephone numbers represents a profile with very limited benign explanation.
The consistency of this TTP set over three-plus years is itself analytically relevant. The same tooling documented by Mandiant in 2022 remains in active use in Q1 2026. This suggests the program has encountered insufficient friction from existing controls, which is expected, given that most organizations have no detection capability at the interview layer. Background checks, skills assessments, and identity verification services are not instrumented to observe the device and network signals described here.
Attribution confidence: Moderate-to-high, based on TTP alignment with the published body of DPRK IT worker research. imper.ai does not claim definitive attribution absent additional corroborating intelligence.
Detection Guidance
The following is intended for security practitioners and teams responsible for pre-employment verification or insider threat programs that cover the hiring pipeline.
Astrill VPN: Maintain and query against published Astrill VPN exit IP blocklists. Any candidate session originating from a known Astrill exit node during a screening or interview process should be flagged for manual review. Do not rely on self-reported or configured location.
Latency and network proximity: Where feasible, implement network proximity or BGP-level origin checks against the candidate’s claimed or configured location. Latency is a physical property that VPNs cannot fully obscure — a VPN exit node can make a session appear US-based, but it cannot increase the round-trip time between the candidate’s device and infrastructure near their true physical location. A session presenting as US-based but exhibiting anomalously low latency to East Asian infrastructure is a non-spoofable signal of physical presence in that region, regardless of the configured or stated location.
Identity signal stacking: Treat the combination of a newly registered email account and a VoIP phone number as a low-trust identity profile requiring additional verification. Neither is individually conclusive. The combination, particularly alongside network anomalies, is a strong composite indicator.
Signal correlation is necessary: No single indicator in this TTP set is sufficient for a confident assessment. Detection requires correlating device, network, and identity signals simultaneously. Organizations relying on resume screening, background checks, or skills assessments as the primary control will not surface the indicators described in this brief. These are network and device-layer signals that require dedicated instrumentation at the screening stage.
References
- Google Cloud / Mandiant — Mitigating the DPRK IT Worker Threat (September 2024) https://cloud.google.com/blog/topics/threat-intelligence/mitigating-dprk-itworker-threat
- Unit 42 / Palo Alto Networks — Global Companies Are Unknowingly Paying North Koreans (November 2024) https://unit42.paloaltonetworks.com/north-korean-it-workers/
- Spur.us — Astrill VPN and DPRK Remote Worker Fraud (December 2024) https://spur.us/blog/astrill-vpn-and-dprk-remote-worker-fraud
- any.run — Lazarus Group IT Workers Investigation (December 2025) https://any.run/cybersecurity-blog/lazarus-group-it-workers-investigation/
- Team Cymru — Uncovering DPRK Remote Workers (June 2025) https://www.team-cymru.com/post/uncovering-dprk-remote-workers
- Microsoft Security Blog — Jasper Sleet: North Korean Remote IT Workers’ Evolving Tactics (June 2025) https://www.microsoft.com/en-us/security/blog/2025/06/30/jasper-sleet-north-korean-remote-it-workers-evolving-tactics-to-infiltrate-organizations/
- Recorded Future — PurpleBravo’s Targeting of the IT Software Supply Chain (January 2026) https://www.recordedfuture.com/research/purplebravos-targeting-it-software-supply-chain
- GitLab Threat Intelligence — North Korean Tradecraft (February 2026) https://about.gitlab.com/blog/gitlab-threat-intelligence-reveals-north-korean-tradecraft/