Author: Jordan Pierce

Defending against Browser Extension Impersonation
Understanding the Rise of Rogue Browser Extensions Have you ever wondered how secure your browser extensions really are? Rogue browser extensions pose a significant threat to endpoint security, when they can be manipulated to steal sensitive information or act as conduits for more invasive attacks. These imperceptible threats highlight the growing concerns of extension identity […]
Read more
Impersonating Medical Device Technicians (IoT)
The Imperative of Robust Identity Verification in IoT Medical Device Security How can organizations ensure the safety and authenticity of their digital interactions where AI-driven deception is becoming increasingly sophisticated? This question is at the forefront of discussions around cybersecurity, particularly within mission-critical sectors like healthcare. With the rapid evolution of technology, threats are constantly […]
Read more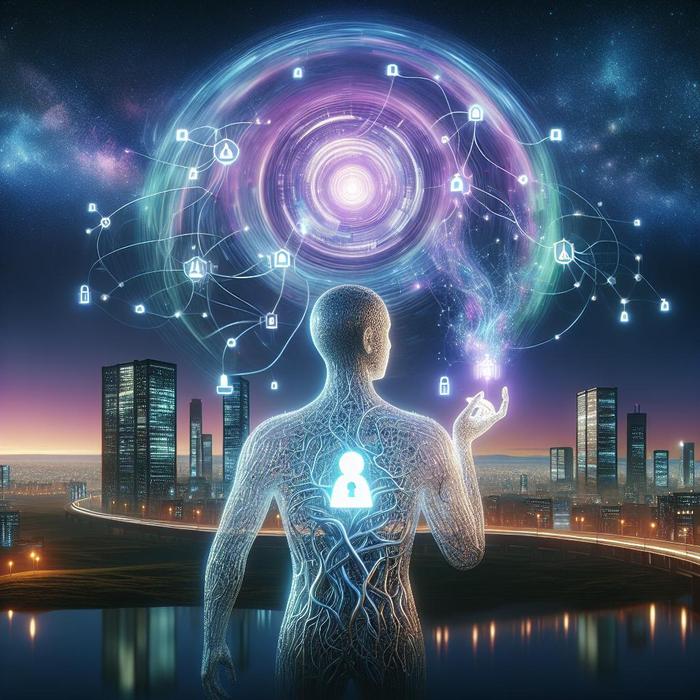
Managing Identity for Automated AI Agents (Bots)
Why Is Real-Time Identity Verification Crucial in AI? Imagine where you can’t trust your own eyes or ears. This isn’t science fiction; it’s the present-day challenge posed by AI-driven deepfake and social engineering threats. Organizations face an uphill battle against these advanced deceptive tactics—especially when they affect identity and access management (IAM). But there’s hope […]
Read more
No-Code Identity Verification for E-commerce
The Role of Identity Verification in Safeguarding E-commerce How can e-commerce businesses thrive while ensuring robust security measures to combat sophisticated AI threats? This question is crucial with digital retail continues to grow, and with it, the challenges of fraud and data breaches persist. The advent of AI-driven identity verification has transformed cybersecurity, providing seamless, […]
Read more
Biometric Cold-Storage for Executive Recovery
Real-Time Identity Verification: A Combat Strategy Against AI-driven Deception Have you ever wondered how organizations can safeguard themselves from the rapidly evolving AI-driven threats that are becoming increasingly sophisticated? Identity verification is not just an additional layer of security but a cornerstone of any robust cybersecurity strategy. With AI technology continues to advance, it becomes […]
Read more
Governance of Identity in Industrial Metaverse
The Strategic Importance of Identity Management in Industrial Metaverse How can organizations ensure the veracity of their communications where digital interactions are rapidly evolving? Industrial metaverse is reshaping in which businesses operate, enabling virtual collaboration on a scale that was previously unimagined. However, with this innovation comes an increased risk of identity and access management […]
Read more
Deepfake Audio in High-Stakes Legal Arbitrations
How Vulnerable are Legal Arbitrations to AI-driven Deepfake Threats? Where artificial intelligence is increasingly influencing various industries, one might wonder about the implications for legal arbitrations. How significant is the threat posed by AI-driven deepfakes to such high-stakes environments? With technology continues to evolve, so too do the threats associated with it. Deepfake technology, while […]
Read more
Defining Identity Fraud ROI for Stakeholders
How Can Organizations Combat AI-driven Deepfake and Social Engineering Attacks? Identity theft and fraud have evolved into sophisticated forms with the rise of AI technologies. This evolution has brought forth a pressing need for organizations to focus on identity and access management (IAM) that proactively addresses security concerns through real-time, identity-first strategies. With digital continuously […]
Read more
Real-Time Cross-Check of Identity Attributes
Understanding the Pervasiveness of AI-Driven Threats Are your organization’s defenses equipped to verify user identity effectively in sophisticated AI-driven threats? Where digital interactions are integral to mission-critical operations, the ability to detect and prevent fraud at its inception is paramount. Sophisticated social engineering attacks leverage advancements like AI-generated deepfakes to manipulate traditional security systems, demanding […]
Read more
Moving to a Zero-Trust Identity Framework
Understanding the Rising Complexity of Identity Verification What strategies can organizations implement to protect themselves against AI-driven deepfake and social engineering attacks? With cyber threats continue to evolve, the management of identity and access management (IAM) becomes crucial. Threats require a zero-trust identity framework that emphasizes an identity-first approach to enhance security and build trust […]
Read more
Bypassing MFA with Real-Time Session Proxies
Understanding Threats MFA Proxy Attacks Are your organization’s defenses truly prepared for increasingly sophisticated multi-factor authentication (MFA) proxy attacks? A profound question, given how these threats have evolved, exploiting weaknesses in identity and access management systems. At the forefront of modern cyber threats lies the complexity of real-time bypass techniques and session theft technology, which […]
Read more
Fake Urgent Security Patch Email Phishing
Understanding the Risks of Emergency Patch Scams How secure is your organization against AI-driven threats masquerading as legitimate communications? A new breed of scams—such as emergency patch scams—aims to exploit vulnerabilities quickly and effectively. These sophisticated threats, often cloaked as urgent updates or security patches, are designed to manipulate victims into granting access to sensitive […]
Read more
Just-In-Time (JIT) Identity Verification
Unmasking Threats: The Power of Just-In-Time Identity Verification How secure is your organization’s digital identity management? Where deepfakes and AI-driven social engineering are becoming increasingly sophisticated, the need for robust identity verification cannot be overstated. Just-In-Time (JIT) Identity Verification emerges as an essential tool in safeguarding mission-critical sectors, preventing infiltration by verifying identities on demand. […]
Read more
Ensuring Ethical Use of Biometric Data
Understanding the Ethical Implications and Responsibilities of Biometric Data Use How can organizations harness the power of biometric data while ensuring ethical standards and protecting user privacy? The potential of biometric data in streamlining identity verification (IDV) processes and enhancing security measures is vast. Yet, it brings profound ethical questions and responsibilities regarding its usage. […]
Read more
The Rise of Identity-First Security
Why Is Identity Verification the New Security Perimeter? Isn’t it fascinating how our understanding of security is undergoing a fundamental shift? Organizations across the globe are waking up to the stark reality that traditional security measures are becoming increasingly inadequate. With digital evolves, the emphasis is moving towards an identity-centric defense, transforming identity verification into […]
Read more
Implementing Phishing-Resistant MFA
Understanding the Imperative for Modern Identity Security How can organizations effectively safeguard their digital interactions? This is a question I grapple with daily. The sophistication of cyberattacks, particularly AI-driven ones, necessitates a shift towards proactive and robust identity security measures. The Rising Threat of AI-Driven Attacks Cybercriminals are increasingly employing advanced methods, such as deepfake […]
Read more