Author: Cole Matthews

Protecting the Passwordless Login Flow from Spoofing
The Critical Importance of Secure Authentication Practices What measures do organizations implement to protect themselves from increasingly sophisticated digital threats? With cybercriminals advance their tactics, businesses across sectors are under pressure to strengthen their defenses, particularly concerning identity verification and social engineering prevention. A key target is the protection of passwordless login systems. Increasing reliance […]
Read more
Decentralized Identifiers (DID) for ESG Reporting
Building Trust in ESG Reporting with Decentralized Identifiers How can companies ensure the integrity of their ESG reporting where sophisticated AI-driven threats are rapidly evolving? This question is more pressing than ever when organizations face increasing scrutiny over their environmental, social, and governance (ESG) credentials. With the rise of artificial intelligence, especially tools capable of […]
Read more
Analyzing Micro-Expressions for Deepfake Video IDV
Decoding the Power of Micro-Expression Detection in AI-Driven Threats How can organizations safeguard their digital frontiers against the sophisticated rise of AI-driven threats? With technology advances, so do the methods of those looking to exploit it. Among the most formidable challenges is the advent of AI-created audio and visual deceptions, which require novel solutions to […]
Read more
Verifiable Credentials for Third-Party Access
Strengthening Organizational Security with Verified Credentials Have you ever wondered how secure the access points into your organization truly are? With AI-driven deepfake and social engineering attacks grow in sophistication, the management of identity and access management (IAM) becomes crucial for safeguarding trust in digital interactions. The strategic oversight provided by Chief Information Security Officers […]
Read more
Managing Identity Friction for Senior Execs
Balancing Executive Security and User Experience How can organizations ensure a seamless executive security experience while preventing sophisticated cyberattacks? Striking this balance becomes crucial amid the rising tide of AI-driven identity threats. Senior executives often face unique challenges in managing their digital footprints, necessitating both enhanced protection and an intuitive user experience. The Sophistication of […]
Read more
Digital Identity Wallets for Employees
Securing the Future: How Real-Time AI-Driven Identity Verification Protects Employees Are your organization’s digital interactions genuinely safe? Safeguarding identities is crucial to maintaining trust. Leveraging AI to detect and prevent deepfake and social engineering attacks at their source is becoming the gold standard for securing employee identities and ensuring verified credentials. The Rising Threats of […]
Read more
Certificate-Based Identity for IoT Devices
The Strategic Importance of Device Certificates in IoT Identity Security How do we establish trust where digital interactions often blur the line between real and manipulated? This question is at the heart of IoT identity security. When organizations continue to embrace the Internet of Things (IoT) for its unparalleled connectivity and operational efficiency, the associated […]
Read more
Protecting Against Real-Time Account Porting
Proactive Measures to Combat Account Porting Threats Have you ever questioned the integrity of your organization’s communication channels and wondered if they’re susceptible to AI-driven manipulation? This is a prevalent concern among many cybersecurity professionals, especially where adversaries continue to evolve their tactics. In particular, the rise of account porting fraud and the potential for […]
Read more
Enforcing MFA for Third-Party Vendors
Securing Third-Party Access: A Crucial Step in Cyber Defense How confident are you in your organization’s control over third-party vendor access? With cyber threats continue to evolve, organizations across sectors are grappling with sophisticated AI-driven attacks like deepfakes and social engineering. With such threats looming, managing identity and access through robust vendor MFA enforcement has […]
Read more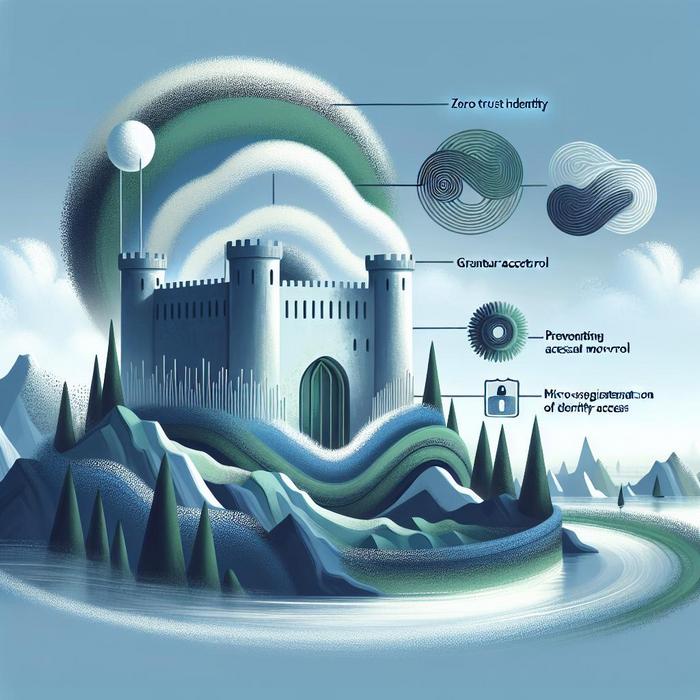
Micro-segmentation of Identity Access
Why is Achieving Zero Trust Identity Paramount for Organizations? With cyber threats increasingly leverage artificial intelligence and sophisticated tactics, organizations find themselves in a constant battle to secure their digital identities. The concept of zero trust identity has emerged as an indispensable defense mechanism, ensuring only authenticated and authorized users can access sensitive information. But […]
Read more
Securing Private Wealth Management Identities
Protecting High Net Worth Individuals from AI-Driven Threats Have you ever considered the risk of someone impersonating you? For those managing private wealth or working in high-stakes environments, this is becoming an increasingly important consideration. The convergence of artificial intelligence (AI) and social engineering has transformed security threats, especially for high net worth individuals and […]
Read more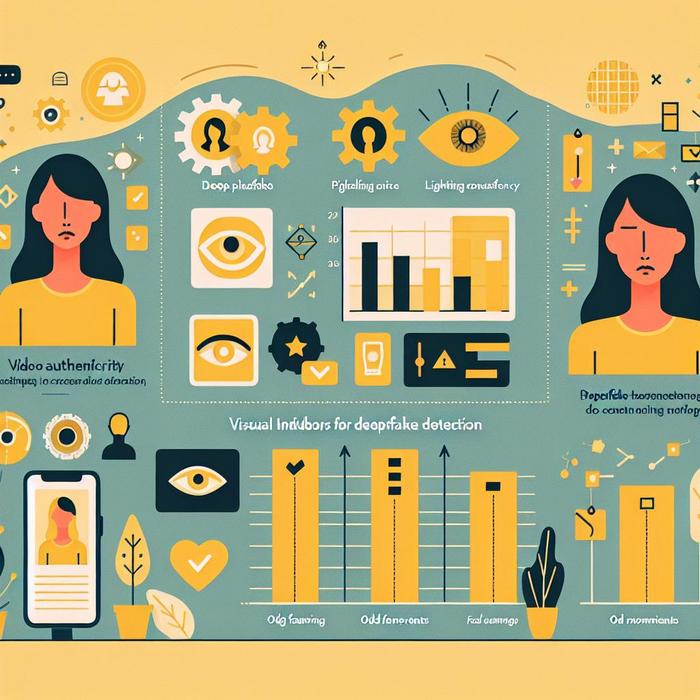
Visual Indicators for Deepfake Detection
Understanding AI-Driven Identity Threats How can organizations effectively combat the sophisticated threats posed by AI-driven fake content? With an industry specialist, the focus on identity verification is paramount for professionals across various sectors. The growing concern about AI-enhanced impersonations emphasizes the need for robust identity and access management (IAM) strategies, particularly in mission-critical industries. The […]
Read more
Zero Trust Identity Architecture
Understanding Zero Trust Identity Architecture How can organizations safeguard themselves against increasingly sophisticated threats? This pivotal question guides the strategic implementation of zero trust identity architecture in contemporary cybersecurity practices, reinforcing identity perimeter defenses with continuous authentication. With cyber threats evolve, particularly those driven by AI, the need for robust, real-time countermeasures is paramount. Professionals […]
Read more
Insurance for Impersonation
The Growing Threat of AI-Driven Impersonation Attacks How prepared are organizations to deal with the evolving threat of AI-driven impersonation attacks? This is a question that many Chief Information Security Officers (CISOs), Chief Information Officers (CIOs), Risk Officers, and IT professionals grapple with daily. While these threats continue to advance in sophistication, the importance of […]
Read more