Stop shadow workforce
before it stops you.
The person you hired isn’t always the person doing the work.
imper.ai continuously verifies who is actually behind the account, every time it matters,
so unverified and unknown operators don’t go undetected inside your workforce.

Establish the baseline
imper.ai captures infrastructure-layer telemetry at a one-time identity-binding moment, either at hire (with imper.ai for Hiring) or at secure enrollment for the existing workforce. This becomes the reference for every verification that follows.
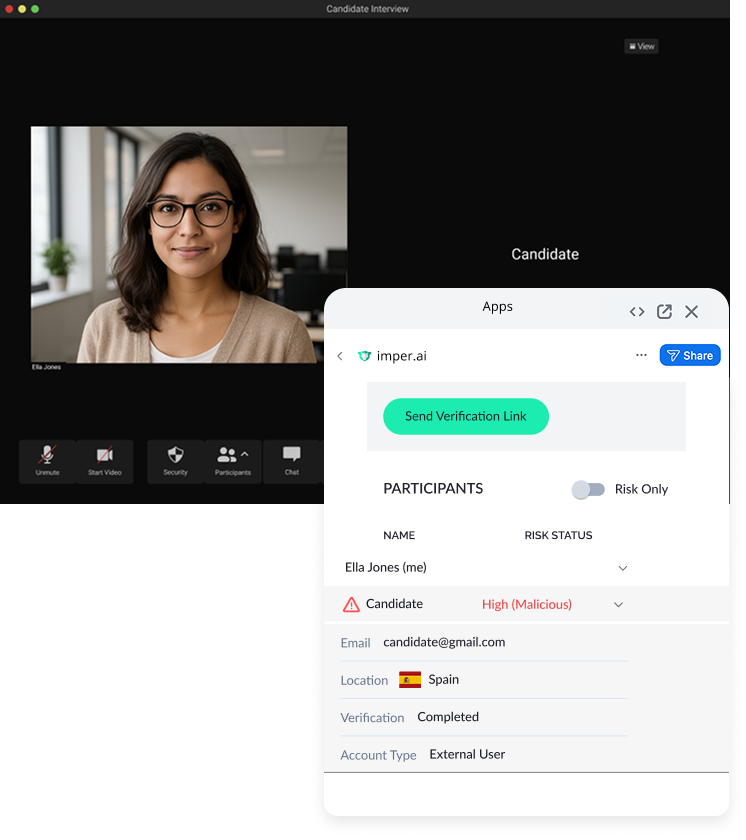
Verify at every high-risk moment
imper.ai embeds into existing IDP, MFA, and PAM workflows. When an employee performs a privileged action, accessing a code repository, approving a wire transfer, escalating into a sensitive system, the Impersonation Detection Engine runs a silent infrastructure check inside the step-up. No new prompt for the user. No new tool to deploy.
Re-verify on your policy
Trigger continuous workforce verification at the cadence you set: every two weeks, every month, every six months. The same infrastructure check runs against the established baseline. Drift surfaces immediately.
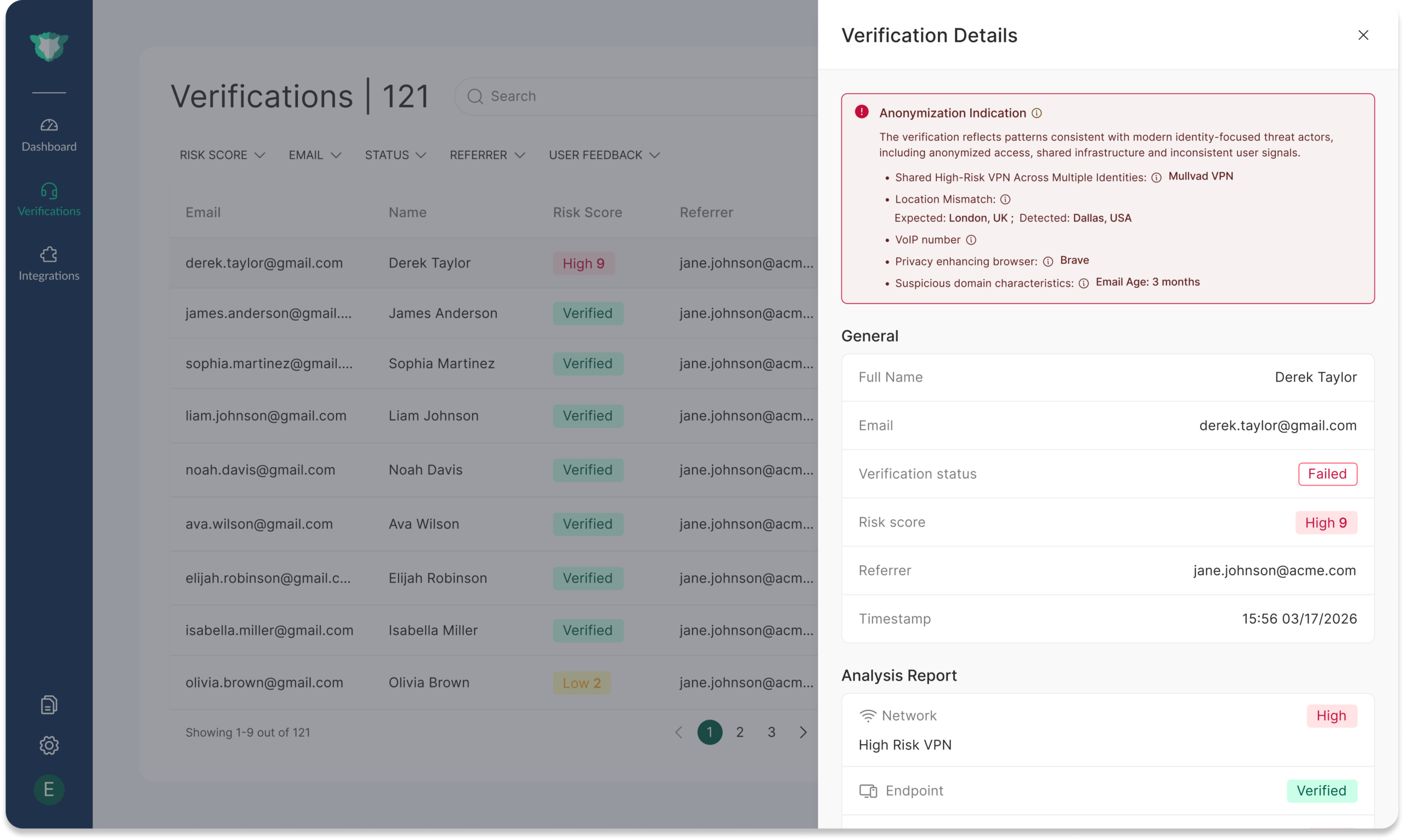
Multi-layered workforce identity assurance
imper.ai detects attacker-controlled environments by analyzing infrastructure signals across the interaction, including device integrity, virtualization artifacts, remote control tooling, and network anomalies.
By correlating hundreds of real-time signals, imper.ai exposes impersonation attempts before credentials are issued or access is granted.
