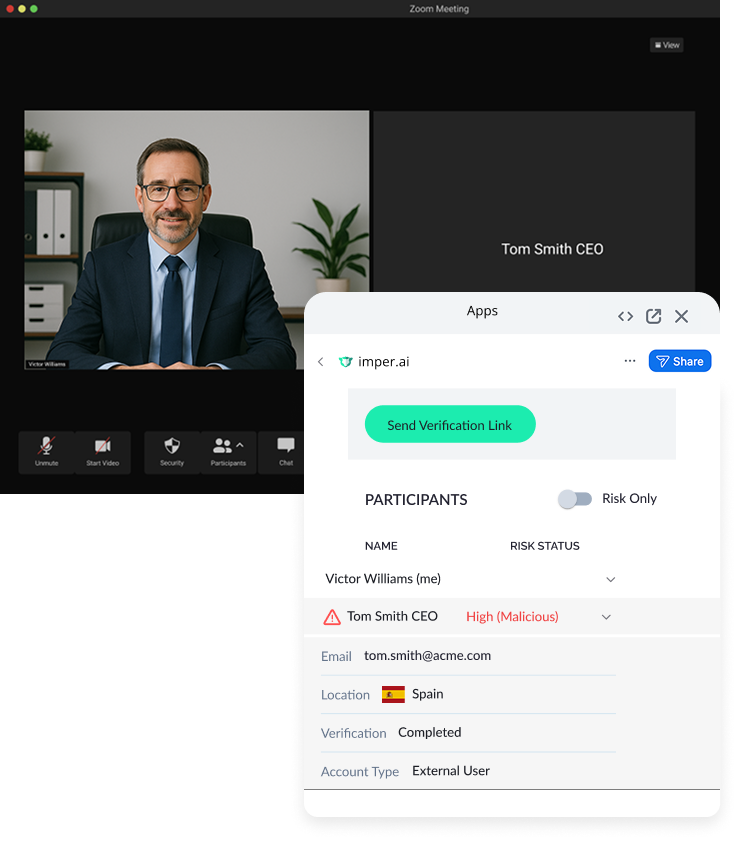
Stop hackers pretending to be your CEO
AI lets attackers clone your leadership team in seconds. imper.ai spots what hackers can’t hide: the network, device, and behavioral markers that prove who’s real, protecting your executives and your brand from digital impostors.
Try imper.ai now

Arup falls victim to $25m video scam
We have all heard about the video call with senior management that prompted an Arup employee to transfer $25 million. But senior management was never on the line.
Read full articleYou trust your team. Attackers exploit that.
Attackers no longer rely on simple phishing. They impersonate executives and employees inside collaboration tools to trigger approvals, reset credentials, and escalate privileges – deepfakes may be used. Often they aren’t.
What makes these attacks succeed is a verification gap: high-trust identity moments where authentication can’t be relied on.
imper.ai verifies the human behind high-risk executive and employee interactions by analyzing infrastructure and behavioral signals that attackers cannot fake.
Your teams collaborate normally.
Impersonation stops before access occurs.
Shut down collaboration tool phishing
Attackers hijack trusted accounts to send meeting invites, payment requests, and file shares that trigger identity changes or credential theft. imper.ai detects attacker-controlled environments behind collaboration activity and flags compromised sessions before damage spreads.
Compromised accounts are flagged before damage is done.
Detect C-suite
impersonation
AI lets attackers clone your leadership team’s voice and face with 97% accuracy. imper.ai doesn’t look at what’s said; it analyzes the digital fingerprints behind the conversation, spotting the network and device anomalies deepfakes can’t hide.
Only authentic voices make it into your boardroom.
Prevent employee
impersonation
When attackers steal logins or session tokens, they blend in like insiders. imper.ai cross-checks real-time device and identity signals against your organization’s known patterns, exposing impostors.
Real employees get through. Fakes don’t.

Communication
detected
imper.ai verifies the person behind the high-risk interaction or request within your existingcollaboration tools, capturing digital fingerprints—device, network, and digital identity signals—from each interaction in real time.
Authenticity
verified
The system presents you with a risk score and lets you know if the person on the other end has an environment matching adversarial techniques used when hiding their true identity. You can determine whether it’s best to drop the call or continue but make further validation checks.
Trust
reinforced
Verified communications move forward seamlessly!
Multi-layered workforce identity assurance
imper.ai analyzes the forensic markers hackers and social engineers can’t hide — from device fingerprints and network intelligence to digital identity. By correlating hundreds of real-time security signals, it exposes hidden impersonation attempts before fraud or data loss occurs.
See how it worksStop CEO impersonation scams before they start
Real-time identity prevention helped a luxury retailer protect itself when hackers used GenAI deepfakes to impersonate C-suite execs and attempt a 7-figure wire fraud.

